Chapter 1: Learn how pervasive consumer concerns about data privacy, unethical ad-driven business models, and the imbalance of power in digital interactions underscore the need to build trust through transparency and regulation.
Chapter 8: Learn how AI’s rapid advancement and widespread adoption present both opportunities and challenges, requiring trust and ethical implementation for responsible deployment. Key concerns include privacy, accountability, transparency, bias, and regulatory adaptation, emphasizing the need for robust governance frameworks, explainable AI, and stakeholder trust to ensure AI’s positive societal impact.
Content in this chapter
- Defining Trust
- Introducing the Iceberg Trust Model
- Development Methodology
- The Contextual Moderation Layer
- 1. Above the Waterline: The Agency Layer
- 2. Above the Waterline: The Engineering Layer
- 3. The Governance Layer
- 4. Below the Waterline: The Institutional Layer
- The Dynamic Process Layer
- Empirical Validation
- Data Context
Today’s digital economy has an enormous potential to transform most of the aspects of our lives. The World Wide Web removes barriers to market entry, develops new, disruptive business models and eventually dissolves traditional values such as brick-and-mortar shops. Technology breaks the barriers between organizations, countries, and time zones. The way to modernity is characterized by a social change that “disembeds” individuals out of their traditional social relationships and localized interaction context (Giddens, 1995).
Every day, fresh start-up companies develop new perspectives on issues of our daily lives and propose often disrupting solutions. The consumer is faced with technologies and social concepts (such as the sharing economy) that are new and unknown. Digital trust disengages itself to an ever larger extent from the known concept of trust in persons and generalizes in institution-based trust (Luhmann, 1989). The iceberg approach to digital trust pays attention to different components of trust and provides a framework that allows marketing professionals to understand how trust is engendered.

Ever since the World Wider Web became a global phenomenon, scientists from a wide range of disciplines try to make the trust construct comprehensible. These studies all build on the broad scientific work from a more analogue world. Deutsch has developed one of the most fundamental definitions for trust (1962): He defines a framework in which an individual faces two aspects. First, the individual has a choice between multiple options that result in outcomes that it perceives as either positive or negative. Second, the individual acknowledges that the actual result depends on the behaviour of another person. Deutsch also mentions that the trusting individual perceives the effect of a bad result as stronger than the effect of a positive outcome. This corresponds to the findings of the prospect theory discussed in chapter 2.
Trust is the willingness of a party to be vulnerable to the actions of another party based on the expectation that the other will perform a particular action important to the trustor, irrespective of the ability to monitor or control that other party“.
(Mayer et al.)
Thus, trust is built if a person assumes the desired beneficial result is more likely to occur than a bad outcome. In this context, there is no possibility to influence the process. The following example illustrates this: a mother leaves her baby to a babysitter. She is aware that the consequences of her choice depend heavily on the behaviour of the babysitter. In addition, she knows that the damage from a bad outcome of this engagement carries more weight than the benefit of a good outcome. Important factors in the trust equation are missing control, vulnerability and the existence of risk (Petermann, 1985).
Multiple options and diverse scenarios lead to ambiguity and risk. According to Lumann, individuals must eventually reduce complexity to decide in such situations. Trust is a mechanism that reduces social complexity. This context is best captured in the definition of trust developed by Mayer, Davis and Schoorman (1995: 712).
Trust can be an efficient help to overcome the agency dilemma. In economics, the principal-agent problem describes a situation where a person or entity (the agent) acts on behalf of another person (the principal). Due to information asymmetry, which is omnipresent in digital markets, the agent can either act in the interest of the principal or not by acting, for example, selfishly. Trust can solve such problems by absorbing behavioural risks (Ripperger, 1998). Screening and signalling activities are often inefficient in situations where information asymmetry exists due to high information costs. Trust can reduce such agency costs (including imminent utility losses). It can increase the agent’s intrinsic motivation to act in the principal’s interest.
You must trust and believe in people, or life becomes impossible.
(Anton Chekhov)
A trust relationship, as such, can be seen as a principal-agent relationship. The relationship between a trusting party and a trusted party is built on an implicit contract. Trust is provided as a down payment by the principal. The accepting agent can either honour this ex-ante payment or disappoint the principal.
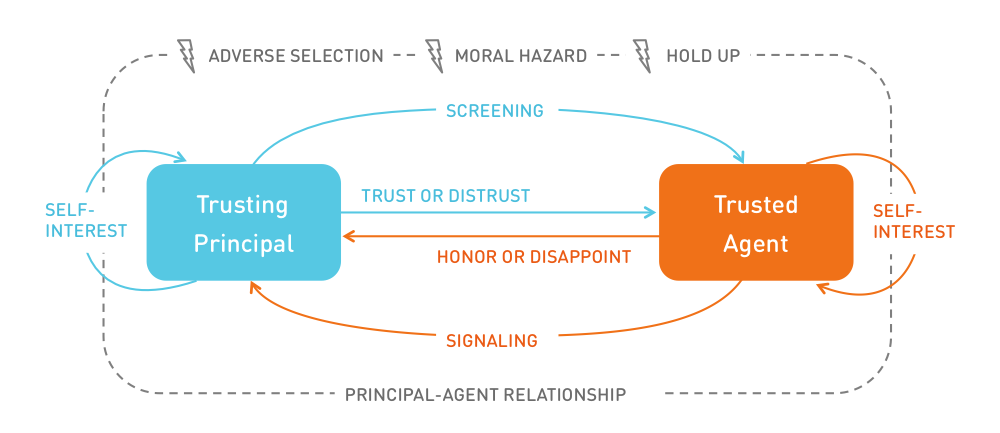
According to the principle-agent theory a trusting party faces three risks:
Adverse Selection: When selecting an agent, the principal faces the risk of choosing an unwanted partner. Hidden characteristics of an agent or their service are not transparent to the principal before the contract is made. This leaves room for the agent to act opportunistically.
Moral Hazard: If information asymmetry occurs after the contract has been closed (ex post), the risk of moral hazard arises. The principal has insufficient information about the exertion level of the agent who fulfills the service. External effects, such as environmental conditions, can influence the agent’s actions.
Hold Up: This type of risk is particularly relevant for the discussion about the use of personal data. It describes the risk if the principal makes a specific investment, such as providing sensitive data. After closing the contract, the agent can abuse this one-sided investment to the detriment of the principal. The subjective insecurity about the agent’s integrity stems from potentially hidden intentions.
The described risks can be reduced through signalling and screening activities. Signalling is a strategy by which agents communicate their nature and authentic character. The provision of certification and quality seals is used to signal activities. On the other hand, a principal seeks to identify an agent’s true nature through screening activities. However, screening is only effective if signals are valid (the agent actually owns this characteristic) and if the absence of such a signal indicates the lack of this trait.
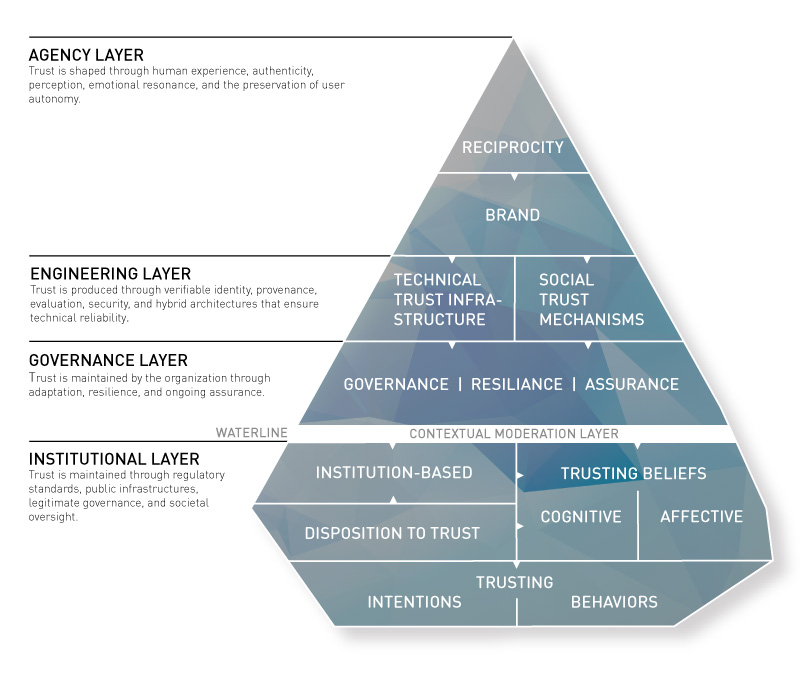
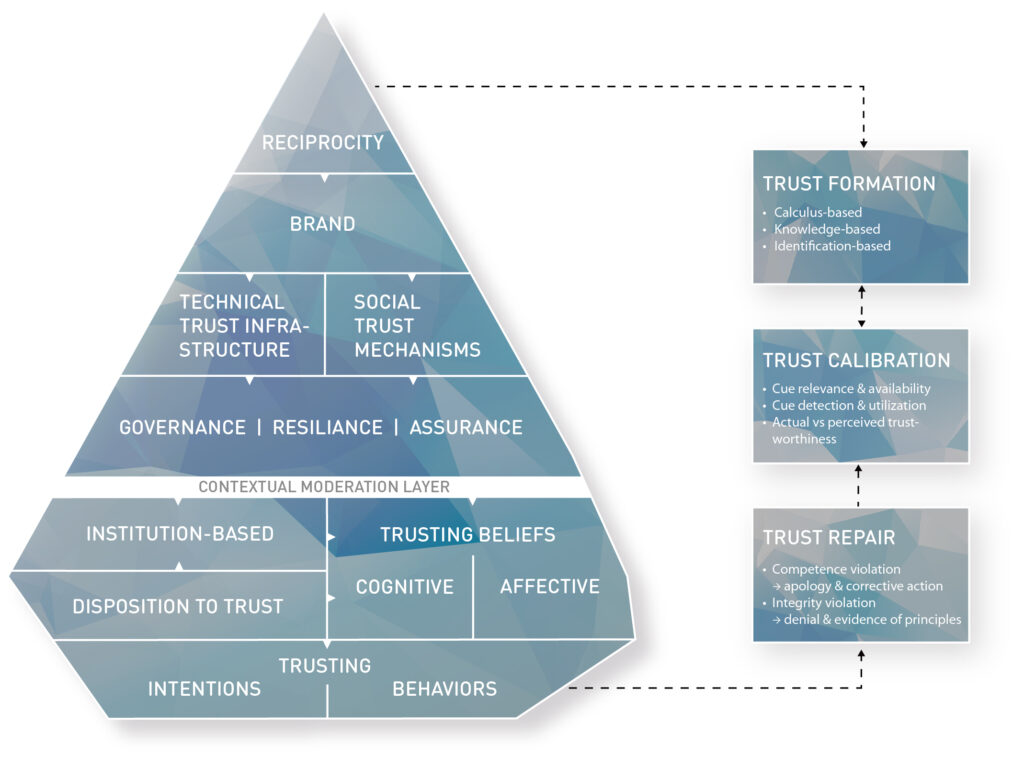
Our trust model resembles the shape of an iceberg.
The iceberg metaphor works in many different ways:
First of all, trust must be seen as a precious good. It is hard to build, but it can be lost very quickly. This makes it both a key differentiator to win against the competition and a potential pitfall that can easily destroy organizations. The Volkswagen emissions scandal has demonstrated how quickly trust is lost. It showed that even strong brands from traditional brick-and-mortar businesses can become severely damaged. The Internet accelerates this process. Bad news or reviews are spread at light speed around the globe, and once negligible pieces of information can cause harmful shitstorms to spiral out of control. Like an iceberg in the open sea, trust issues must be recognized early, and marketers must sail elegantly around such perils. On the other hand, trust is vital. Ongoing melting of the polar ice caps will inevitably raise sea levels and put coastal areas at risk. Similarly, if the trust factor is neglected, organizations miss out on potential business opportunities and risk being sunk by the competition.
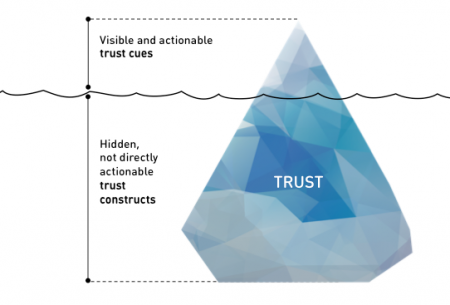
Second, the sheer size of an iceberg usually remains unknown to the observer. This is due to ice’s lower density than that of liquid water. Hence, only one-tenth of the volume of an iceberg is typically above the water level. This reflects that most of the determinants of trust are less known, not understood, or simply invisible. Moreover, it is difficult to manipulate those constructs. Trust, therefore, is often built when no one is looking. For companies, this means there are limited but essential options to address information asymmetry in digital markets.
Just like freezing water and forming an iceberg takes time, building trust usually takes time. The primary way to gain trust is to earn it by developing and nurturing relationships with customers and future prospects. Companies can and must have control over the quality and intensity of the customer experience if they want to influence the customer’s level of trust. Opportunities to shape the experience exist at touchpoints in the customer decision lifecycle. This model, however, focuses on understanding and engendering initial trust.
How can the multi-disciplinary determinants of digital trust be organized into a unified conceptual framework that (a) distinguishes observable trust cues from latent psychological constructs, (b) is grounded in established trust theory across disciplines, (c) is operationalizable for assessment, and (d) accommodates the specific trust dynamics of AI systems?
The Iceberg Trust Model was developed through a two-phase methodology.
Phase 1 used Design Science Research (Hevner et al., 2004) to construct the four-layer framework architecture and five design principles. The framework was evaluated through case analysis of real-world trust phenomena, including the Swiss e-ID referendum, AI marketing campaigns by Coca-Cola and Apple, and governance failures such as the Deloitte Australia incident.
Phase 2 applied a grounded-theory literature review (Wolfswinkel, Furtmueller, and Wilderom, 2013) to operationalize the framework into a structured, multi-level classification scheme. This is a literature-synthesis method that adapts the three-phase coding procedure of Strauss and Corbin (1998) to a defined interdisciplinary corpus, rather than classical grounded theory on fresh empirical fieldwork. A corpus of 34 primary sources spanning seven disciplines was coded in three phases: open coding produced approximately 250 trust-related concepts; axial coding consolidated these into 15 emergent categories; and selective coding integrated them around the core category of digital trust formation. The resulting ontology comprises 10 constructs and 124 trust cues. Theoretical saturation was reached at source 25 of 34.
Phase 1: Framework Architecture (Design Science Research)
The four-layer architecture (Agency, Engineering, Governance, Institutional) and five design principles were developed using Design Science Research (Hevner et al., 2004). Problem identification drew on systematic literature analysis spanning 1964 to 2025. Solution design synthesized systems theory (Luhmann, 1979), resilience engineering (Hollnagel et al., 2006), and sociotechnical systems research. Evaluation used case analysis of real-world trust phenomena: the Swiss e-ID referendum (institutional trust failure), contrasting AI marketing approaches by Coca-Cola and Apple (brand trust divergence), and governance failures exemplified by the Deloitte Australia incident (governance trust collapse).
Phase 2: Framework Construction (Grounded-Theory Literature Review)
The framework’s four layers were operationalized into a structured multi-level classification scheme of 10 constructs and 124 trust cues using a grounded-theory literature review (Wolfswinkel et al., 2013). The procedure adapts the three-phase coding process (Strauss and Corbin, 1998) to a defined interdisciplinary corpus. Throughout the rest of this chapter, the term framework refers to this classification scheme. The word ontology is reserved for future formalization per Gruber (1993), which is identified as follow-on work (see Limitations).
A corpus of 34 primary sources spanning seven disciplines (organizational psychology, information systems, economics, governance, resilience engineering, social psychology, and human-computer interaction) was coded through three sequential phases. Theoretical saturation was reached at source 25 of 34, after which no new categories emerged from the remaining 9 sources.
Limitations and Future Work
This chapter establishes construct validity through theoretical grounding and internal consistency checking. It does not claim predictive validity. Known limitations:
- Not a PRISMA systematic review. Source selection was purposive from the interdisciplinary trust literature. Any missed source would need to establish a 16th axial category to change the framework’s structure; the conceptual coverage plateau at source 25 provides a principled stopping criterion.
- Single-coder analysis. Coding was performed by a single researcher. The documented constant-comparison protocol and paradigm mapping provide partial mitigation, but formal inter-rater reliability cannot be reported. Expert panel validation (Delphi method) and independent dual coding of a random source subset are identified as priorities for future work.
- Role of the author’s prior work. The R1-R5 framework that organized the literature selection is articulated in prior work by the author (Glinz, 2015, 2025, 2026). These prior articulations are cited as announcement documents; the theoretical weight is carried by external, independently validated sources (Mayer et al., 1995; McKnight et al., 2002; Lankton et al., 2015; Sollner et al., 2016; and others). The R1-R5 framework is a selection scaffold, not a load-bearing theoretical contribution claimed by the present chapter.
- Governance construct derivation. The Governance, Resilience and Assurance construct was developed through a design-science synthesis (Hevner et al., 2004) of four external frameworks: NIST AI RMF 1.0 (2023), the EU AI Act (2024), the IIA Three Lines Model (2020), and resilience engineering (Hollnagel, Woods, and Leveson, 2006). Prior author contributions articulated the synthesis; the external frameworks carry the theoretical weight. Independent external validation of the governance cues is identified as a priority for future work.
- Conceptual coverage, not theoretical saturation. The corpus reached a conceptual coverage plateau at source 25 of 34. This is not saturation in the Glaserian sense, which would require iterative theoretical sampling driven by ongoing analysis.
- Construct, not formal ontology. The work is a multi-level classification scheme, not a formal ontology in the Gruber (1993) / Guarino and Welty (2002) sense. Formal axiomatization, OntoClean metaproperty analysis, and OWL/RDFS representation are identified as future work.
- No predictive validation. Whether the framework predicts real-world trust outcomes (user behavior, market impact, regulatory action) has not been tested and requires separate empirical investigation. Preliminary evidence from adjacent trust literature (Beldad, de Jong, and Steehouder, 2010; Kim, Ferrin, and Rao, 2008; Kaplan, Kessler, Brill, and Hancock, 2023, Human Factors) is consistent with the above/below waterline distinction but does not constitute direct validation of the present framework.
LLM-assistance disclosure. Draft composition and copy-editing of this chapter used Claude (Anthropic) and ChatGPT (OpenAI). All factual claims, source attributions, and analytical decisions were verified against primary sources by the author. Coding decisions were made by the author, not the LLM. The author takes full responsibility for the final text.
The Literature Corpus: 34 Sources Across Five Trust Conceptualizations
The model draws on 34 primary academic sources spanning 1964 to 2025, organized by five distinct trust conceptualizations (R1 through R5). This structure ensured that no single discipline dominated the analysis and that all types of digital trust relationships were represented. Each conceptualization required at least two sources: a definitional anchor and at least one empirical or review study. An additional 17 cross-cutting frameworks (EU AI Act, NIST AI RMF, IIA Three Lines Model, WEF Earning Digital Trust, ISACA DTEF, and others) were referenced for specific constructs but not coded line-by-line.
Trust in Persons and Organizations
8 sources
Foundational interpersonal trust: competence, benevolence, integrity, social exchange, signaling.
Mayer et al. (1995), McAllister (1995), Blau (1964), Spence (1973), Fukuyama (1995), Rousseau et al. (1998), Giffin (1967), Deutsch (1976).
Trust in Digital Economy Agents
10 sources
E-commerce trust typology, institution-based trust, empirical cue validation.
McKnight et al. (2002), Hoffmann et al. (2014), Gefen et al. (2003), Dinev and Hart (2006), Pavlou and Gefen (2004), Ripperger (2003), McKnight et al. (1998), Gefen (2000), Koufaris and Hampton-Sosa (2004), Hendrikx et al. (2015).
Trust in AI Systems
10 sources
AI governance, resilience engineering, trustworthiness assessment (TrAM).
Schlicker et al. (2025a, 2025b), Hollnagel et al. (2006), NIST (2023), Glikson and Woolley (2020), Lukyanenko et al. (2022), Muir (1994), Hoff and Bashir (2015), Choung et al. (2022), Thiebes et al. (2021).
Trust in the Interface
4 sources
Relational intelligence, rapport-building, anthropomorphic trust activation.
Bickmore and Cassell (2001), Zierau et al. (2021), Vossing et al. (2022), Van Pinxteren et al. (2019).
Trust and Personality
2 dedicated + 4 cross-contributing
Individual differences, dispositional trust, personality-trust links.
Riedl (2022), Szalma and Taylor (2011). Cross-contributing: McKnight et al. (2002), Hoffmann et al. (2014), Hoff and Bashir (2015).
The Coding Process: Three Sequential Phases
Open Coding
Each of the 34 primary sources was read in full. For every trust-relevant concept encountered, a code was created with a label, definition, source passage, and discipline of origin. This process produced approximately 250 discrete trust-related concepts across seven disciplinary domains.
Axial Coding
Concepts were compared pairwise through constant comparison (Glaser and Strauss, 1967) and grouped into categories based on shared properties and functional relationships. Each category was mapped using Strauss and Corbin’s paradigm model (causal conditions, context, intervening conditions, action strategies, consequences). This phase produced 15 emergent categories.
Selective Coding
All 15 categories were integrated around the core category of “digital trust formation in sociotechnical systems.” This integration revealed a fundamental distinction: some categories describe observable signals (above the waterline), others describe latent psychological states (below the waterline), one functions as an environmental moderator (the water), and two describe temporal processes (the currents).
From 15 Categories to 10 Constructs
The 15 axial categories were consolidated into the framework’s final architecture through nine documented design decisions. The full decision log, with explicit rationale and reference to the external sources carrying the theoretical weight (Mayer et al., 1995; McKnight et al., 2002; Lankton et al., 2015; Sollner et al., 2016; NIST, 2023; EU AI Act, 2024; Hollnagel et al., 2006; and others), is presented below. Each mapping was justified by empirical evidence, theoretical grounding, or both.
Categories 1-4
Trustworthiness Beliefs, Dispositional Trust, Institutional Trust, and Trust Intentions became the below-waterline constructs.
Latent psychological states, not directly observable. Faithful to the McKnight et al. (2002) trust typology.
Category 5
Brand and Reputation became Brand, above waterline in the Agency Layer. Grounded in signaling theory (Spence, 1973) and brand-trust research (Chaudhuri and Holbrook, 2001), together with Hoffmann, Lutz, and Meckel (2014), who report that brand cues drive behavioral intentions through a pathway distinct from trusting-beliefs formation.
Category 6
Fair Exchange and Reciprocity became Reciprocity, above waterline in the Agency Layer. Grounded in Blau’s (1964) social-exchange theory and in Hoffmann, Lutz, and Meckel (2014), who report that reciprocity cues have a strong effect on trusting beliefs relative to other cue categories tested. Specific path coefficients should be verified against the primary source; see Limitations.
Categories 7-8
Technical Infrastructure and Social Mechanisms became Technical Trust Infrastructure and Social Trust Mechanisms, above waterline in the Engineering Layer. Following Sollner et al.’s (2016) distinction between technology-mediated and socially-mediated trust.
Category 9
Governance, Resilience, Accountability became an above-waterline Governance Layer. Organized into three sub-dimensions: Adaptive Governance, Organizational Resilience, and Continuous Digital Assurance.
Category 10
Perceived Risk became the Contextual Moderation Layer at the waterline. Risk is a property of the situation, not of the trustor or trustee (Mayer et al., 1995). Extended with four contextual parameters: Risk Magnitude, Cultural Trust Radius, Domain Sensitivity, and User Segment.
Category 11
Affective Trust became Affective Trusting Beliefs (ATB), below waterline. Cognition-based and affect-based trust are empirically distinct constructs that follow different pathways and predict different outcomes (McAllister, 1995; Glikson and Woolley, 2020).
Categories 12-13
Trust Dynamics and Trust Repair became the Dynamic Process Layer, a temporal overlay comprising three processes: Formation, Calibration, and Repair. These are not static constructs but dynamic forces that continuously reshape the iceberg.
Categories 14-15
Distrust and AI-Specific Dimensions were distributed across existing constructs. Distrust was operationalized via the Trust State Vector (tracking trust and distrust independently on each Mayer dimension). AI-specific dimensions were integrated through the dual-lens TB architecture and distributed cues across R, B, TI, and GOV.
Conceptual Coverage Assessment
A critical question for any literature-based classification scheme is: how do we know the corpus was sufficient? This study does not claim theoretical saturation in the Glaserian sense (which would require iterative theoretical sampling driven by ongoing analysis). It reports a conceptual coverage plateau: the point at which additional sources no longer produce new axial categories. The answer lies in theoretical saturation, the point at which additional sources no longer produce new categories.
In this study, category emergence plateaued at source 25 of 34 (Hollnagel, Woods and Leveson, 2006): subsequent sources enriched existing categories but did not produce new ones. At that point, all 15 axial categories had been established. The subsequent 9 sources (Schlicker et al. 2025a/b, Bickmore and Cassell, Zierau et al., Vossing et al., Van Pinxteren et al., Riedl, Szalma and Taylor) contributed exclusively to enriching existing categories with new properties and dimensions, but no new categories emerged.
This trajectory is consistent with the thematic-plateau pattern reported by Guest, Bunce and Johnson (2006), in which new themes typically cease to emerge between 12 and 30 sources. A complementary empirical coverage assessment was performed: the L2 cue taxonomy was applied to a database of 1,500+ real-world trust incidents, showing that the cues are sufficient to describe the diversity of observed trust violations across industries and geographies. This is a coverage check of the taxonomy, not a predictive validation of the framework; the incidents were classified using the same taxonomy, so the check speaks to classificatory adequacy rather than to external predictive validity. Independent predictive validation (structural equation modeling, prospective behavioral studies) is identified as a priority for future work (see Limitations).
The source-by-category emergence matrix documents a conceptual coverage plateau for the 15 categories and 10 constructs with respect to the reviewed corpus. This is evidence of comprehensiveness relative to the literature sampled; it is not a claim of theoretical saturation in the Glaserian sense, nor of external predictive validity.
Trust is not generated through a single mechanism; it arises from the interaction of human perception, technical architectures, organisational safeguards, and institutional infrastructures. To understand how AI systems can be designed and governed responsibly, trust must be conceptualized as a multi-level socio-technical construct that involves human agency, engineering robustness, governance assurance, and institutional legitimacy. Trust-centric design sits at the intersection of these layers, translating structural guarantees into meaningful user experiences.
Trust-centric design serves as a bridge between human psychology, engineering infrastructure, and institutional governance. It translates deep structural assurances (identity, provenance, oversight) into signals that users can understand intuitively, making trust both visible and tangible. Effective trust-centric design requires clarity about authorship, contextual transparency, and visible human oversight. It must ensure that users feel empowered and respected, even when interacting with advanced automated systems.
This integrative perspective highlights that trust cannot be achieved through interface design, infrastructure, or regulation alone. Trust emerges only when the agency, engineering, governance, and institutional layers reinforce one another. When design aligns with verifiable architectures and legitimate governance, digital systems gain both emotional credibility and structural reliability.
The combined framework demonstrates that trustworthy AI requires coordination across three interdependent layers.
Human trust is strengthened when emotional cues align with structural assurances. Engineering trustworthiness is meaningful only when users understand and experience it. Institutional legitimacy is anchored in both broader societal expectations and long-term governance.
Perceived risk is not a construct in the ontology but the environmental moderator that makes the entire model meaningful. In the iceberg metaphor, perceived risk is the water.
Just as seawater surrounds the iceberg and determines what is visible above the surface, the contextual environment surrounds every trust assessment. The water is not uniform. A warm current raises the waterline, exposing more of the iceberg: in high-trust cultures, users accept cues at face value and require less verification. A cold current pushes the waterline down, submerging more of the structure beneath scrutiny: in low-trust environments, users demand verifiable evidence before extending trust. The depth of the water represents the stakes involved. The salinity reflects domain-specific expectations. And the currents represent the processing patterns of different user segments.
The water around the iceberg has four measurable properties that modulate how cues are perceived and weighted:
Risk Magnitude
Cue scrutiny depth. Higher risk means more cues are examined and higher thresholds are required. In low-risk situations (shallow water), most of the iceberg is visible: users do not scrutinize trust cues carefully. In high-risk situations (deep water), users examine every available cue (Mayer et al., 1995; Kim et al., 2008).
Cultural Trust Radius
Which cue categories are weighted. High-trust-radius cultures weight Brand more heavily and accept institutional assurance more readily. Low-trust-radius cultures weight Governance and Technical Trust Infrastructure cues, demanding verifiable evidence over reputation (Fukuyama, 1995; Hofstede, 2001).
Domain Sensitivity
Cue threshold levels. Healthcare and financial services demand higher Governance and Technical Trust Infrastructure cue satisfaction than entertainment or social media (Bart et al., 2005).
User Segment
Cue processing mode. Digital natives use heuristic processing (relying on Brand and design quality); digital immigrants use systematic processing (scrutinizing Reciprocity and Technical Trust cues). Age, technology experience, and digital literacy modulate which cues are detected and how they are weighted (Hoffmann et al., 2014).
With the water properties defined, we can now examine the ice itself. The five above-waterline constructs represent the observable trust signals that organizations can design, deploy, and measure. They are grouped into three architectural layers: the Agency Layer (Reciprocity and Brand, shaped by human experience), the Engineering Layer (Technical Trust Infrastructure and Social Trust Mechanisms, shaped by system design), and the Governance Layer (organizational oversight and assurance). Each construct carries a set of L2 cues that function as specific, actionable trust signals.
The iceberg model suggests five clusters of trust cues that sit at the tip of the iceberg: Reciprocity, Brand, Technical Trust Infrastructure, Social Trust Mechanisms, and Governance cues. Each cluster holds a set of trust signals or trust design patterns that marketing professionals can consider to engender trust. Chapter Two and the discussion of the principal-agent problem highlight the importance of trust cues in online transactions. “Perceptions of a trust cue trigger preestablished cognitive and affective associations in the user’s mind, which allows for speedy information processing” (Hoffmann et al., 2015, 142).
The iceberg framework identifies, for each above-waterline trust construct, a set of trust cues (between 17 and 23 per construct, totaling 124 across all ten constructs). The list was developed by first reviewing existing frameworks from the research literature and then integrating contemporary digital trust considerations. We applied a constant-comparison protocol (Glaser and Strauss, 1967; Charmaz, 2006) to group cues into five distinct constructs, testing construct boundaries so that each cue has a distinct scope within its construct and the set of cues covers the major aspects of digital trust identified in the corpus. This is an internal consistency check, not a claim of formal ontological axiom checking in the Gruber (1993) or Guarino and Welty (2002) sense. This method combines established ideas (such as transparency, warranties, and community moderation) with newer considerations (such as AI disclosures and quantum-safe encryption).
However, the list has limitations. It represents a snapshot in time and may not capture every emerging cue as digital trust evolves. Additionally, while the MECE framework helps clarify categories, some cues (e.g., 3rd party data sharing or sustainability commitments) can naturally span multiple constructs depending on context, and decisions on allocation involve some subjective judgment. This means the list should be seen as a flexible starting point for discussion rather than an exhaustive, immutable taxonomy.
Reciprocity:
Reciprocity is a social construct that describes the act of rewarding kind actions by responding to a positive action with another positive action. The benefits to be gained from transactions in the digital space originate in the willingness of individuals to take risks by placing trust in others who are regarded to act competently, benevolently and morally. A fair degree of reciprocity in the exchange of data, money, products and services reduces user’s concerns and eventually induces trust (Sheehan/Hoy, 2000). A user that provides personal data to an online service – actively or passively –perceives this as an exchange input. They expect an outcome of adequate value. A fair level of reciprocity is reached through the transparent exchange of information for appropriate compensation. The table below shows the most relevant signals or strategic elements that establish positive reciprocity.
THE 20 RECIPROCITY CUES (R01-R20)
R01: Value and Fair Pricing | R02: Exchange Transparency | R03: Accountability and Liability | R04: Terms, Pricing and Subscription Transparency | R05: Warranties and Guarantees | R06: Customer Service and Support | R07: Delivery and Fulfillment Excellence | R08: Refund, Return and Cancellation | R09: Recognition and Rewards | R10: Error and Breach Handling | R11: Dispute Resolution and Mediation | R12: User Education and Guidance | R13: Acknowledgment of Contributions | R14: Micropayments and In-App Transparency | R15: Algorithmic Fairness and Non-Discrimination | R16: Proactive Issue Resolution | R17: Informed Defaults | R18: Data Reciprocity | R19: AI Explanation Reciprocity | R20: Privacy-Value Exchange Visibility
R01: Value & Fair Pricing
A business needs to offer fair reciprocal benefits directly relevant to the data it collects and stores. If the business uses information not necessary to the service being provided, additional compensation must be considered. Because of their bounded rationality, consumers are often likely to trade off long-term privacy for short-term benefits.
Eventually, trust is about encapsulated interest, a closed loop of each party’s self-interest.
Ensuring users/customers receive clear, tangible benefits (value) at a reasonable or transparent cost.
Engender: Users feel respected when transparent pricing aligns with the value delivered.
Erode: Hidden fees, overpriced tiers, or unclear costs can drive user frustration and distrust.
R02: Transparency & Explainability
Fair and open information practices are essential enablers of reciprocity. Users must be able to quickly find all relevant information. This leads to a reduction in actual or perceived information asymmetry. Customer data advocacy can require altruistic information practices.
Disclosing policies, processes, and decision‐making (e.g., algorithms) clearly so users understand how outcomes or recommendations are reached. This includes fairness and transparency regarding 3rd-party data sharing.
Engender: Users appreciate open communication, which reduces suspicion.
Erode: Opaque “black box” operations lead people to suspect manipulation or unfair treatment.
R03: Accountability & Liability
Users expect that access to their data will be used responsibly and in their best interests. If a company cannot meet these expectations or if an unfavourable incident occurs, businesses must demonstrate accountability. This requires processes and organizational precautions that enable quick, responsible responses.
Compliance is either a state of being in accordance with established guidelines or specifications, or the process of becoming so. The definition of compliance can also encompass efforts to ensure that organizations abide by industry regulations and government legislation.
In an age when platforms offer branded services without owning physical assets or employing the providers (e.g., Uber doesn’t own cars and doesn’t employ drivers), issues of accountability are increasingly complex. Transparency and commitment to accountability are increasingly strong indicators of trust.
. Being upfront about who is responsible when things go wrong and having mechanisms in place to take corrective action.
Engender: Owning mistakes and compensating users when appropriate builds trust.
Erode: Shifting blame or hiding mishaps erodes confidence and loyalty.
R04: Terms & Conditions (Legal Clarity)
Standard legal information, such as Terms and Conditions and security and privacy policies, must be made proactively accessible. Users need to be informed about the information collected and used. The consistency of this content over time is an important signal that helps build trust.
Clearly stated user agreements, disclaimers, and legal obligations define the formal relationship between the company and the user.
Engender: Straightforward T&Cs (short, plain language) help users feel informed.
Erode: Long, incomprehensible, or deceptive “fine print” fosters suspicion.
R05: Warranties & Guarantees
Warranties and guarantees support the perception of fair reciprocity and, therefore, signal trustworthiness. Opportunistic behaviour will entail expenses for the agent.
Commitments ensuring quality or functionality of products/services, often with money‐back or replacement policies.
Engender: Demonstrates company confidence in their offering, signaling reliability.
Erode: Denying legitimate warranty claims or offering poor coverage breaks trust.
R06: Customer Service & Support
Pre- and after-sales service, as well as any other touch point that allows a user to contact an agent, is a terrific opportunity to shape the customer experience. Failures in this strategic element are penalized with distrust and unfavourable feedback.
Reliability is relatively easy to demonstrate online. It is critical to respond quickly to customer requests.
Responsive, empathetic help channels (phone, chat, email) that address user questions and problems effectively.
Engender: Timely, helpful support reassures users that the company cares about them.
Erode: Unresponsive or unhelpful support creates frustration and alienation.
R07: Delivery & Fulfillment Excellence
Reliability, speed, and accuracy in delivering digital or physical products/services to end users.
Engender: Meeting (or exceeding) delivery promises confirms reliability.
Erode: Late or missing deliveries, or misleading timelines, undermine user confidence.
R08: Refund, Return & Cancellation Policies
Fair and user‐friendly processes for returns, refunds, or canceling subscriptions.
Engender: Demonstrates respect for user choice, reduces perceived risk.
Erode: Excessive hurdles, restocking fees, or strict no‐refund policies create mistrust.
This trust cue refers to the concept of social capital. This kind of capital refers to connections among individuals – social networks and the norms of reciprocity and trustworthiness that arise from them. The cue is similar to social translucence (please refer to the category “Social Trust Mechanisms”). However, it highlights instead the importance of the collective value rather than the social impact of certain behaviours.
R09: Recognition & Rewards
Loyalty programs, badges, and acknowledgment systems that reward continued engagement and signal that the organization values returning users.
R10: Error & Breach Handling
Transparent, timely communication when things go wrong, combined with clear remediation steps and genuine accountability for failures.
R11: Dispute Resolution & Mediation
Accessible, fair processes for resolving disagreements between users and the organization, including escalation paths and independent mediation options.
R12: User Education & Guidance
Proactive efforts to help users understand how data is used, how services work, and how to make informed decisions about their engagement.
R13: Acknowledgment of Contributions
Recognition of user feedback, content contributions, and community participation as valued inputs rather than free labor.
R14: Micropayments & In-App Transparency
Clear disclosure of costs associated with in-app purchases, premium features, and subscription tiers, avoiding surprise charges or confusing pricing structures.
R15: Algorithmic Fairness & Non-Discrimination
Commitment to ensuring that automated decisions do not systematically disadvantage particular groups based on protected characteristics.
R16: Proactive Issue Resolution
Anticipating and addressing potential problems before users encounter them, rather than waiting for complaints to trigger reactive fixes.
R17: Informed Defaults
Setting default configurations that protect user interests (privacy-preserving, data-minimizing) rather than maximizing organizational data extraction.
R18: Data Reciprocity
Providing users with tangible value derived from the data they share, closing the loop between data provision and benefit delivery.
R19: AI Explanation Reciprocity
When AI systems influence user outcomes, providing proportionate explanations that match the stakes involved in the decision.
R20: Privacy-Value Exchange Visibility
Making the trade-off between personal data provision and service benefits explicit and comprehensible, so users can make informed consent decisions.
Brand
A second powerful signal promoting trusting beliefs is an entity’s brand. A company makes a specific commitment when investing in its brand, reputation, and awareness. Since brand building is a costly endeavor, consumers perceive this signal as very trustworthy. Capital invested in a brand can be considered a stake at risk with every customer interaction and transaction. Whether an investment pays off or is lost depends heavily on a company’s true competency. Strategic elements such as brand recognition, image, and website design should trigger associations in the user’s cognitive system, prompting a feeling of familiarity.
“Brands arose to compensate for the dehumanizing effects of the Industrial Age” (Rushkoff, 2017). They are essentially symbols of origin and authenticity.
THE 18 BRAND CUES (B01-B18)
B01: Brand Ethics and Moral Values | B02: Brand Image and Reputation | B03: Recognition and Market Reach | B04: Familiarity and Cultural Relevance | B05: Personalization | B06: Brand Story and Narrative | B07: Design Quality and Aesthetics | B08: Consistency and Cohesion | B09: Heritage and Longevity | B10: Cultural Impact | B11: Localized Expressions | B12: Purpose and Mission | B13: Branded Experiences | B14: ESG Commitments | B15: Costly Signal Investment | B16: AI Model Provenance | B17: Developer Reputation | B18: Digital Experience Innovation
B01: Brand Ethics & Moral Values
The moral stance a brand publicly claims and consistently upholds (e.g., integrity, fairness, honesty).
Engender: Strong ethical standards reassure users of brand integrity.
Erode: Ethical lapses (cover‐ups, scandals) quickly destroy trust and cause reputational damage.
B02: Brand Image & Reputation
The identity of a company triggers associations that together constitute the brand image. It is the impression in the consumers’ minds of a brand’s total personality. Brand image is developed over time through advertising campaigns with a consistent theme and is authenticated through the consumers’ direct experience.
In the digital age, brands must focus on delivering authentic experiences and get comfortable with transparency.
Overall public perception of the brand’s character, reliability, and standing in the market.
Engender: Consistent positive image fosters user loyalty and pride in association.
Erode: Negative PR or repeated controversies undermine confidence.
B03: Recognition & Market Reach
Brand recognition is the extent to which a consumer or the general public can identify a brand by its attributes, such as its logo, tagline, packaging, or advertising campaign. Frequent exposure has been shown to elicit positive feelings towards the brand stimulus.
Consumers are more willing to rely on large and well-established providers. Digital consumers prefer brands with a broad reach. Search engine marketing is a relevant element that influences a brand’s relevance and reach. Many new business models rely on a competitive advantage in the ability to generate leads through search engine optimization (SEO) and search engine advertising (SEA).
The degree to which the brand is widely known and recognized across regions and demographics.
Engender: Familiarity can reduce perceived risk and enhance trust.
Erode: If scandals or controversies accompany a wide reach, broad exposure amplifies distrust.
B04: Familiarity & Cultural Relevance
Design Patterns & Skeuomorphism: Skeuomorphism makes interface objects familiar to users by using concepts they recognize. Use of objects that mimic their real-world counterparts in how they appear and/or how the user can interact with them. A well-known example is the recycle bin icon used for discarding files.
California Roll principle: The California Roll is a type of sushi developed to familiarize Americans with unfamiliar food. People don’t want something truly new; they want the familiar done differently.
Privacy by Design advances the view that the future of privacy cannot be assured solely by compliance with legislation and regulatory frameworks; rather, privacy assurance must become an organization’s default mode of operation. It is an approach to systems engineering that takes privacy into account throughout the whole engineering process. Privacy needs to be embedded by default throughout the architecture, design, and construction of the processes.
Design Thinking describes a paradigm – not a method – for innovation. It integrates human, business, and technical factors into problem formulation, problem solving, and design. The user (human) centred approach to design has been extended beyond user needs and product specification to include the „human-machine-experience“.
How naturally the brand’s products/services fit into local customs, language, and user contexts.
Engender: Users resonate with solutions tailored to their cultural norms.
Erode: Ignoring cultural nuances can lead to alienation or offense.
B05: Personalized Brand Experience
Digital customers are very demanding about the relevance of a product, service, or piece of information. Mass customization and personalization foster a good customer experience. The ability to process large amounts of data enables individualized transactions and aligns production with pseudo-individual customer requirements.
Through personalization, a customer feels like they are being treated as a segment of one. Service providers can offer individual solutions and thereby increase perceived competency by providing better, faster access to relevant information. Personalization works best in markets with fragmented customer needs.
Tailoring brand touchpoints (marketing, app interactions) so users feel recognized as individuals.
Engender: Users appreciate relevant, personal engagement.
Erode: Over‐personalization or privacy intrusions can feel creepy or manipulative.
B06: Brand Story & Narrative
Ever since the days of bonfires and cave paintings, humans have used storytelling to foster social bonding. Content marketing and storytelling done right are elemental means to engender trust. Well-constructed narratives attract attention and build an emotional connection. As trust in media, organizations, and institutions diminishes, stories offer an underappreciated vehicle for fostering these connections and, eventually, establishing credibility. Attributes of stories that build trust are genuine, authentic, transparent, meaningfu,l and familiar.
The brand’s history, origins, and overarching story that communicates purpose and authenticity.
Engender: A compelling, consistent narrative humanizes the brand and builds empathy.
Erode: Contradictions between stated story and actual practice (greenwashing, etc.) damage credibility.
B07: Design Quality & Aesthetics
The quality of a brand’s digital presence (web, mobile, etc.) can foster brand reputation and enhance brand recognition. High site quality signals that the company has the required level of competence.
Important design qualities include usability, accessibility, and the resulting user experience.
A fundamental paradigm leading the design process is the process of “Privacy by Design”:
Privacy by Design advances the view that the future of privacy cannot be assured solely through compliance with legislation and regulatory frameworks; rather, privacy assurance must become an organization’s default mode of operation (privacy by default). It is an approach to systems engineering that takes privacy into account throughout the whole engineering process.
Privacy needs to be embedded by default throughout the architecture, design, and construction of the processes. The demonstrated ability to secure and protect digital data needs to be part of the brand identity.
Done right, this design principle increases the perception of security. This refers to the perception that networks, computers, programs, and, in particular, data are always protected from attack, damage, or unauthorized access.
The visual identity and user experience design that shape a recognizable “look and feel.”
Engender: High‐quality design suggests professionalism and attention to detail.
Erode: Shoddy, inconsistent, or dated design signals carelessness or lack of refinement.
B08: Brand Consistency & Cohesion
Uniform messages, tone, and imagery across all channels (web, mobile, social media, physical stores).
Engender: Consistency implies reliability and coherence.
Erode: Inconsistent experiences (conflicting statements or design) can confuse and unsettle users.
B09: Heritage & Longevity
The brand’s history, track record, and sustained market presence as evidence of enduring reliability and institutional commitment.
B10: Cultural Impact
The brand’s influence on broader cultural conversations, social movements, or industry standards beyond its immediate commercial footprint.
B11: Localized Expressions
Adaptation of brand messaging, visual identity, and product offerings to resonate with local customs, languages, and cultural expectations.
B12: Purpose & Mission
A clearly articulated organizational purpose that connects commercial activity to broader social or environmental goals, providing users with values-based reasons to trust.
B13: Branded Experiences
Immersive, exclusive, or memorable interactions (events, limited editions, flagship experiences) that deepen emotional connection and create shared identity.
B14: ESG Commitments
Demonstrated environmental, social, and governance commitments backed by measurable targets, transparent reporting, and third-party verification.
B15: Costly Signal Investment
Visible, verifiable investments in brand quality, infrastructure, or community that would be economically irrational for a dishonest actor to make (Spence, 1973).
B16: AI Model Provenance
Transparent disclosure of who developed an AI model, what data it was trained on, and under what governance framework it operates.
B17: Developer Reputation
The track record, public credibility, and ethical standing of the individuals and organizations responsible for building and maintaining the AI system.
B18: Digital Experience Innovation
Demonstrated investment in novel digital interactions (immersive interfaces, accessibility features, cross-platform consistency) that signal technical competence and user-centric design.
Human perception alone cannot sustain digital trust without robust technical foundations. The engineering layer conceptualizes trust as a system property that must be measurable, auditable, and verifiable. Technical trust arises from mechanisms such as identity assurance, provenance tracking, cryptographic guarantees, adversarial evaluation, and resilient system architectures. These mechanisms act as Technical Trust Infrastructure, reducing uncertainty, and as Social Trust Mechanisms, preventing harm and misuse.
Modern AI systems introduce distinctive failure modes, including hallucinations, distributional drift, prompt injection, data leakage, and bias amplification, that require continuous evaluation throughout a system’s lifecycle (Antil, 2025; Amodei et al., 2016). Evidence-based controls such as anomaly detection, model monitoring pipelines, data provenance tracking, and bias audits convert trust from a narrative into a demonstrable system attribute.
Distributed digital ecosystems increasingly depend on decentralized trust infrastructures that provide cryptographically verifiable guarantees. Self-Sovereign Identity (SSI), verifiable credentials, and the Trust over IP (ToIP) stack enable privacy-preserving identity exchange and selective disclosure (W3C, 2021; ToIP, 2022). Standards such as C2PA, which enable content to be cryptographically signed at creation, establish provenance, mitigate deepfake-driven misinformation, and preserve epistemic trust online (C2PA, 2022).
Despite the flexibility of large neural models, many trust requirements, including rule consistency, auditability, and transparent reasoning, cannot be ensured by probabilistic systems alone. This limitation has accelerated the adoption of hybrid AI architectures that combine symbolic reasoning, deterministic rule engines, verifiable credential flows, and knowledge graphs with generative models (Marcus, 2020). Such hybrid approaches combine adaptability with predictability, thereby providing the technical reliability demanded in high-stakes or regulated domains.
Technical Trust Infrastructure
Technical Trust Infrastructure is the strategic element that connects the cues processed by the cognitive system with the base of the iceberg. It interfaces with the construct of institution-based trust. It holds innovative strategic elements in the technological space that influence how consumers perceive structural assurance and situational normality. As outlined in Chapter 1, system complexity in a modern digital world increases on a factorial scale. Increasing system complexity, in turn, requires more decentralized control mechanisms (Helbing, 2015). This is why digital consumers must be given more control over their data. It is a matter of time before decentralized user control becomes a legal requirement.
By reinforcing structural assurance and situational normality, the Technical Trust Infrastructure connects to the institution-based trust at the base of the iceberg. Institution-based trust means the user trusts the institution or system because of its supportive structures and the broader context, even if they have no prior personal interaction with it. For instance, a new user on a platform might not yet trust the individual seller (no prior relationship), but if the platform offers strong structural assurances (e.g., escrowed payments, a money-back guarantee) and everything about the site feels “legit” and normal, the user’s institution-based trust is high. The Technical Trust Infrastructure encompasses “technological framework” elements that create this effect. We can think of it as trust by design: it’s about building the trust layer into the digital environment itself.
It’s important to note how the Technical Trust Infrastructure concept reflects a shift toward designing for trust in modern digital strategy. Many companies now invest in features such as two-factor authentication, user control panels for privacy settings, transparent explanations of AI decisions, and consistent user interface guidelines – all of which can be seen as Technical Trust Infrastructure tools that increase users’ confidence in the system. In summary, the Technical Trust Infrastructure is about embedding trustworthiness into the system’s architecture and user experience, so that even unseen processes (such as security algorithms or data-handling practices) translate into a sense of trust for users. Organizations can foster trust by proactively adopting and implementing effective Technical Trust Infrastructure strategies early and with care.
Industry experts increasingly describe digital trust as having two dimensions: explicit and implicit trust (Tölke, 2024). One hypothesis posits that “digital trust = explicit trust × implicit trust”, suggesting that both factors are essential and mutually reinforcing in creating overall trust. While this equation is more conceptual than mathematical, it conveys the idea that if either explicit or implicit trust is zero, the result (digital trust) will be zero.
Digital Trust = Explicit Trust × Implicit Trust
Explicit trust refers to trust that is consciously and deliberately fostered or signaled. It includes any action or information deliberately provided to engender trust. For example, when a platform verifies users’ identities or when a user sees a verified badge or signed certificate, those are explicit trust signals. In access management terms, explicit trust might mean continuously verifying identity and credentials each time before granting access, essentially a “never trust, always verify” approach. An example of explicit trust in practice is a reputation system on a marketplace: a buyer trusts a seller because the seller has 5-star ratings and perhaps a “Verified Seller” badge. That trust is explicitly cultivated through visible data. Another example is an AI system that provides explanations or certifications; a user might trust a medical AI’s recommendation more if an explanation is provided and if the AI model is certified by a credible institution (explicit assurances of trustworthiness).
Implicit trust, on the other hand, refers to trust that is built indirectly or in the background, often without the user’s conscious effort. It stems from the environment and behavior rather than overt signals. Implicit trust typically includes the technical and structural reliability of systems. For instance, a user may not see the cybersecurity measures in place, but if the platform has never been breached and consistently behaves securely, the user develops an implicit trust in it. As one industry report noted, “Implicit trust includes cybersecurity measures to protect digital infrastructure and data from threats such as hacking, malware, phishing and theft” (Tölke, 2024). Users generally won’t actively think “I trust the encryption algorithm on this website,” but the very absence of security incidents and the seamless functioning of security protocols contribute to their trust implicitly. Likewise, consistent user experience and adherence to norms (which tie back to situational normality) build implicit trust. Users feel comfortable and at ease because nothing alarming has happened.
In the field of recommender systems, the distinction between explicit and implicit trust has been studied to improve recommendations (Demirci & Karagoz, 2022). Explicit trust can be something like a user explicitly marking another user as trustworthy (as was possible on platforms like Epinions, where you could maintain a Web-of-Trust of reviewers). Implicit trust can be inferred from behavior. If two users have very similar tastes in movies, the system might infer a level of trust or similarity between them, even if they never explicitly stated it. Demirci & Karagoz have found that these two forms of trust information have “different natures, and are to be used in a complementary way” to improve outcomes (2022, 444). In other words, explicit trust data is often sparse but highly accurate when available (e.g., an explicit positive rating means strong declared trust). In contrast, implicit trust can fill in the gaps by analyzing behavior patterns.
Applying this back to digital trust broadly: Explicit trust × Implicit trust means that to achieve a high level of user trust, a digital system must provide tangible, visible assurances (explicit cues) and invisible, underlying reliability (implicit factors). If a system has only implicit trust (e.g., it’s very secure and well-engineered) but provides no explicit cues, users might not realize they should trust it. Users may feel uneasy simply because there are no familiar signals, even if it’s trustworthy under the hood. Conversely, if a system has many explicit trust signals but lacks actual implicit trustworthiness, users may be initially convinced, but that trust will erode quickly if something goes wrong. The combination is key: users need to see reasons to trust and also experience consistency and safety that justify that trust.
The Technical Trust Infrastructure component of the Iceberg Model, together with the Brand and Reciprocity cues, can be viewed as the embodiment of this dual approach. It provides the technological trust infrastructure (implicit) and often also interfaces with user-facing elements (explicit), such as interface cues or processes that make those assurances evident to the user. For instance, consider an online banking website. The Technical Trust Infrastructure elements would include back-end security systems, encryption, fraud detection (implicit trust builders), and front-end signals like displaying the padlock icon and “https” (encryption explicit cue), showing logos of trust (FDIC insured, etc.), or requiring the user’s OTP (one-time passcode) for login. When done right, the user both feels the site is safe (everything behaves normally and securely) and sees indications that it is trustworthy. In this way, the Technical Trust Infrastructure aligns with the idea that digital trust is the product of explicit and implicit trust factors working together.
It’s worth noting that in cybersecurity architecture, there has been a shift “from implicit trust to explicit trust” in recent years, epitomized by the Zero Trust security modelfedresources.com. Zero Trust means the system assumes no implicit trust, even for internal network actors – everything must be explicitly authenticated and verified. This approach was born of the realization that implicit trust (such as assuming anyone within a corporate network is trustworthy) can be exploited. While Zero Trust is about security design, its rise illustrates a broader trend: relying solely on implicit trust is no longer sufficient. Systems must continually earn trust through explicit verification. However, the end-user’s perspective still involves implicit trust; users don’t see all those checks happening, they simply notice that breaches are rare, which again builds their quiet, implicit confidence. Thus, even in a Zero Trust architecture, the outcome for a user is a combination of explicit interaction (e.g., frequent logins, multifactor auth prompts) and implicit trust (the assumption that the system is secure by default once those steps are done).
In summary, the hypothesis that digital trust equals explicit trust multiplied by implicit trust highlights a crucial principle: trust-by-design must operate on both the visible and invisible planes. It’s not a literal equation for computing trust, but a reminder that product designers, security engineers, and digital strategists need to address human trust at both levels: by providing transparent, deliberate trust signals and by ensuring robust, dependable system behavior.
Note: The multiplicative formula is a conceptual illustration, not an empirically validated equation. The relationship between explicit and implicit trust is more nuanced than simple multiplication. The Contextual Moderation Layer (Section 4) provides a more rigorous framework for understanding how contextual factors modulate trust formation.
As digital ecosystems evolve, a growing chorus of experts argues that true digital trust will increasingly hinge on decentralized user control. In traditional, centralized models, users had to place significant trust in large institutions or platforms to serve as custodians of data, identity, and security. This aligns with what we discussed as institution-based trust (trusting the platform’s structures). However, recurring scandals have eroded confidence and exposed a key limitation: when a single entity holds all the keys (to identity, data, etc.), a failure or abuse by that entity can shatter user trust across the board. Empowering users with more direct control is emerging as a way to mitigate this risk and distribute trust.
One area where this philosophy is taking shape is digital identity management. The conventional approach to digital identity (think of how Facebook or Google act as identity providers, or how your data is stored in countless company databases) is highly centralized. Now, new approaches such as decentralized and self-sovereign identity (SSI) are shifting that paradigm.
In an SSI system, you might have a digital identity wallet that stores credentials issued to you (e.g., a digital driver’s license or a verified diploma). These credentials are cryptographically signed by issuers but are ultimately controlled by the user. By removing centralized intermediaries, users no longer need to implicitly trust a single middleman for all identity assertions; trust is instead placed in open protocols and cryptographic mathematics.
From a user’s perspective, decentralized identity and similar approaches can significantly enhance trust. First, privacy is improved because the user can disclose only the necessary information, or none at all (using techniques like selective disclosure or zero-knowledge proofs), rather than handing over full profiles to every service. Second, there’s a sense of empowerment: the user owns their data and keys. This aligns with rising consumer expectations and data protection regulations (such as GDPR) that promote greater user agency.
A Technical Trust Infrastructure element in the modern sense might be a platform’s integration with decentralized identity standards. By doing so, the platform signals structural assurance in a new form: no single party (including the platform itself) can unilaterally compromise user identity, because identity is decentralized. It also contributes to situational normality over time, as these practices become standard and users become familiar with controlling their data.
Beyond identity, the theme of decentralization appears in discussions of trustworthy AI and data governance. For example, using decentralized architectures or federated learning can assure users that their data isn’t pooled on a central server for AI training, but rather stays on their device (enhancing implicit trust in how the AI operates). Similarly, blockchain technology is often touted as a “trustless” system. It aims to eliminate the need for blindly trusting a central intermediary. Trust is instead placed in a distributed network with transparent rules (the protocol code) and consensus mechanisms. When we say “trustless” in this context, it means the Technical Trust Infrastructure is the network and code itself. If well-designed, users implicitly trust the blockchain system due to its transparency and immutability, and explicit trust is further enhanced by the ability to verify transactions publicly.
It should be noted that decentralized approaches introduce their own complexities. Not every user wants, or is able, to manage private keys securely; for example, doing so introduces a new level of personal responsibility. A balance is needed: usability (which contributes to situational normality) must be designed hand in hand with decentralization. This is again where the Technical Trust Infrastructure plays a role: innovative solutions like social key recovery (where a user’s friends can help restore access to a wallet) or hardware secure modules in phones (to safely store keys) are being developed to make decentralized control viable and friendly. These are technological adaptations to social needs, encapsulated well by the Technical Trust Infrastructure idea.
In summary, the push for decentralized user control is a response to the erosion of trust in heavily centralized systems. By distributing trust and giving individuals more control over their identity and data, the structural assurance of digital services can increase, paradoxically by removing reliance on any single structure and instead trusting open, transparent frameworks. The implication for digital trust is profound: future trust signals might be less about “trust our company” and more about “trust this open protocol we’ve adopted” and “you are in charge of your information.”
If the last decade was about platforms asking users to trust them (often implicitly), the coming years may be about platforms empowering users so that less blind trust is needed. This evolution supports a more sustainable, user-centric approach to digital trust, where control and confidence grow together.
THE 20 TECHNICAL TRUST INFRASTRUCTURE CUES (TI01-TI20)
TI01: Model Cards & Training Documentation | TI02: Hallucination Detection & Mitigation | TI03: UX Familiarity & Interface Conventions | TI04: Adaptive Communication & Responsiveness | TI05: AI System Self-Disclosure | TI06: Trust Maturity Indicators | TI07: User Control & Agency | TI08: Privacy Management & Consent Mechanisms | TI09: Identity & Access Management | TI10: Trustless Systems & Smart Contracts | TI11: Privacy-Enhancing Technologies | TI12: Adaptive Cybersecurity & Fraud Detection | TI13: Auditable Algorithms & Open-Source Frameworks | TI14: Federated Learning & Decentralized Models | TI15: Trust Score Systems & Ratings | TI16: Data Portability & Interoperability | TI17: Trust Influencers (Change Management) | TI18: Generative AI Disclosures | TI19: Algorithmic Recourse & Appeal | TI20: Data Minimization & Privacy-Preserving Analytics
TI07: User Control & Agency
User control is a foundational requirement of trustworthy AI, recognized across regulatory frameworks from the EU AI Act to the NIST AI Risk Management Framework. Shneiderman (2020) argues that human agency in AI interactions is not merely a design preference but a prerequisite for accountability. When users can meaningfully intervene in, override, or opt out of automated decisions, they retain a sense of authorship over outcomes. Without such affordances, systems risk producing learned helplessness and eroding the psychological contract between user and provider.
Mechanisms that provide users with meaningful control to inspect, override, pause, or exit automated processes.
Engender: Providing granular controls (preference dashboards, override toggles, opt-out flows) signals respect for user autonomy and reinforces the perception that the system serves the user rather than constraining them.
Erode: Systems that lock users into automated pipelines with no override path generate frustration and distrust, particularly when outcomes are consequential. Removal of previously available controls is perceived as a breach of implicit agreement.
TI09: Identity & Access Management
Identity and access management (IAM) forms the perimeter through which trust is technically enforced. As Sandhu et al. (1996) established with role-based access control, the principle of least privilege ensures that actors interact only with the resources their role demands. In AI systems, IAM extends beyond human users to encompass service accounts, model endpoints, and automated agents. The integrity of IAM directly determines whether trust assumptions encoded in policy translate into runtime reality.
Robust authentication, authorization, and credential management practices governing access to AI system components, data pipelines, and decision outputs.
Engender: Multi-factor authentication, fine-grained role definitions, and auditable access logs demonstrate that system operators take boundary enforcement seriously, strengthening institutional trust.
Erode: Weak credential policies, overly broad permissions, or unmonitored service accounts create attack surfaces that, once exploited, destroy trust catastrophically and publicly.
TI08: Privacy Management & Consent Mechanisms
Privacy management in AI systems must go beyond regulatory checkbox compliance toward what Nissenbaum (2010) calls “contextual integrity,” where information flows respect the norms of the context in which data was originally shared. Consent mechanisms are the user-facing expression of this principle. The GDPR requirement for freely given, specific, informed, and unambiguous consent sets the legal floor, but genuine trust requires consent architectures that are comprehensible, revocable, and granular enough to match the complexity of modern data processing.
Granular and accessible mechanisms through which users grant, modify, and withdraw consent for data collection and processing by AI systems.
Engender: Layered consent interfaces that let users understand what they are agreeing to, combined with simple revocation paths, build confidence that the organization respects data subjects as partners rather than resources.
Erode: Dark patterns in consent flows, buried opt-out mechanisms, or consent that is technically revocable but practically irreversible signal that privacy commitments are performative, triggering regulatory scrutiny and user backlash.
TI02: Hallucination Detection & Mitigation
Hallucination, the generation of plausible but factually incorrect outputs, represents one of the most distinctive trust threats posed by large language models and generative AI systems. Ji et al. (2023) provide a comprehensive taxonomy distinguishing intrinsic hallucinations (contradicting source material) from extrinsic ones (unverifiable claims). The challenge is compounded by the fluency of hallucinated outputs: users often cannot distinguish confident fabrication from grounded reasoning without external verification infrastructure.
Detection, flagging, and mitigation strategies for hallucinated or confabulated outputs across generative AI components.
Engender: Retrieval-augmented generation, confidence calibration, citation linking, and explicit uncertainty markers demonstrate that the system actively guards against ungrounded claims, reinforcing user confidence in output reliability.
Erode: Undetected hallucinations in high-stakes contexts (medical, legal, financial) cause direct harm and, once discovered, permanently damage credibility. A single well-publicized hallucination incident can define public perception of an entire product category.
TI13: Auditable Algorithms & Open-Source Frameworks
Auditability is the technical precondition for accountability. Raji et al. (2020) demonstrate that algorithmic audits, whether internal or external, require access to model architecture, training procedures, and evaluation criteria. Open-source frameworks lower the barrier to independent scrutiny by enabling third-party reproduction and validation. The tension between proprietary protection and public accountability is a central challenge in AI governance, and the degree to which organizations resolve it in favor of transparency directly shapes stakeholder trust.
Algorithmic decision systems designed to permit independent audit, supported by open-source tooling, reproducible evaluation pipelines, or structured access for external reviewers.
Engender: Publishing model weights, evaluation benchmarks, or structured audit access programs signals confidence in the system and invites the kind of external validation that regulators and civil society organizations increasingly demand.
Erode: Opacity in algorithmic decision-making, particularly when combined with consequential outcomes, invites suspicion. Refusing third-party audit requests or obstructing reproducibility suggests that the organization has something to hide.
TI10: Trustless Systems & Smart Contracts
The concept of “trustless” systems, architectures that enforce commitments through cryptographic proof rather than institutional reputation, originates in distributed ledger technology but has broader implications for AI governance. Werbach (2018) distinguishes between trust in institutions, trust in intermediaries, and trust in code, arguing that smart contracts shift enforcement from discretionary judgment to deterministic execution. In AI contexts, trustless mechanisms can guarantee that data-use agreements, model-access policies, or royalty distributions are honored without requiring faith in any single party.
Cryptographic enforcement mechanisms, smart contracts, or verifiable computation that reduce reliance on institutional trust for compliance assurance.
Engender: Immutable audit trails, automated policy enforcement, and verifiable computation proofs remove the need for stakeholders to “take your word for it,” converting trust from a social judgment into a mathematical guarantee.
Erode: Promising trustless guarantees while retaining backdoor override capabilities, or deploying smart contracts with unaudited vulnerabilities, creates a false sense of security that collapses spectacularly upon discovery.
TI18: Generative AI Disclosures
As generative AI outputs become indistinguishable from human-produced content, disclosure obligations move from ethical nicety to regulatory mandate. The EU AI Act explicitly requires that AI-generated content be labeled as such in specified contexts. Hancock et al. (2020) show that awareness of AI involvement materially changes how recipients evaluate message credibility. Disclosure is not merely about labeling; it encompasses provenance tracking, watermarking, and metadata that allows downstream consumers to assess the origin and reliability of content they encounter.
Clear, consistent, and tamper-resistant disclosure of synthetic origin and the conditions under which AI-generated outputs were produced.
Engender: Proactive disclosure through visible labels, embedded metadata, and content provenance standards (such as C2PA) demonstrates respect for the recipient’s right to know and positions the organization as a responsible actor in the generative AI ecosystem.
Erode: Deploying generative outputs without disclosure, or making disclosures easily removable, enables misuse and exposes the organization to regulatory penalties, reputational damage, and complicity in misinformation.
TI19: Algorithmic Recourse & Appeal
Algorithmic recourse, the ability of individuals to obtain a different outcome by changing actionable input features, is formalized by Ustun et al. (2019) and Karimi et al. (2021) as both a fairness desideratum and a practical right. Appeal mechanisms extend recourse from the technical layer (what inputs to change) to the institutional layer (who to petition and under what process). The EU AI Act mandates human oversight and contestability for high-risk systems, making recourse not optional but legally required in many jurisdictions.
Meaningful recourse pathways for individuals affected by automated decisions, including explanations, actionable guidance, and a structured appeal process with human review.
Engender: Clear recourse pathways, published timelines for appeal review, and documented reversal rates signal that the organization treats automated decisions as provisional judgments subject to correction, not final verdicts.
Erode: Systems that offer no explanation, no path to reversal, and no human escalation route communicate that efficiency outweighs justice. This is the trust failure pattern most likely to generate litigation, media coverage, and regulatory intervention.
TI01: Model Cards & Training Documentation
Structured documentation artifacts (Mitchell et al., 2019) that disclose a model’s intended use, training data composition, evaluation metrics, and known limitations to enable informed deployment decisions.
TI03: UX Familiarity & Interface Conventions
The degree to which an AI system’s interface adheres to established interaction patterns and platform conventions, reducing cognitive load and leveraging existing mental models to lower the threshold for initial trust formation.
TI04: Adaptive Communication & Responsiveness
The capacity of an AI system to adjust its communication style, complexity level, and response format based on user context, expertise, and expressed preferences, sustaining engagement without condescension or opacity.
TI05: AI System Self-Disclosure
Proactive identification by an AI system of its own nature, capabilities, and boundaries, ensuring users understand they are interacting with an automated agent rather than a human operator.
TI06: Trust Maturity Indicators
Observable signals and metrics that allow stakeholders to assess the current maturity level of an organization’s AI trust practices across dimensions such as governance, transparency, fairness, and security.
TI11: Privacy-Enhancing Technologies
Technical mechanisms including differential privacy, homomorphic encryption, secure multi-party computation, and synthetic data generation that enable useful computation over sensitive data while provably limiting disclosure risk.
TI12: Adaptive Cybersecurity & Fraud Detection
Security architectures that employ machine learning to detect anomalous access patterns, adversarial inputs, and novel attack vectors in real time, adapting defensive postures without requiring manual rule updates.
TI14: Federated Learning & Decentralized Models
Training architectures that keep raw data on local devices or within institutional boundaries, transmitting only model updates to a central aggregator, thereby reducing data exposure while enabling collaborative model improvement.
TI15: Trust Score Systems & Ratings
Quantitative frameworks that aggregate multiple trust-relevant signals (compliance status, audit outcomes, incident history, user feedback) into composite scores, enabling comparative assessment and benchmarking across AI systems or providers.
TI16: Data Portability & Interoperability
The ability of users and organizations to extract, transfer, and reuse their data across AI systems and platforms without loss of structure or meaning, reducing vendor lock-in and reinforcing data sovereignty.
TI17: Trust Influencers (Change Management)
Designated roles and communication strategies within an organization that champion trust practices, translate technical safeguards into stakeholder-accessible narratives, and drive adoption of responsible AI norms across teams.
TI20: Data Minimization & Privacy-Preserving Analytics
The principle and practice of collecting and retaining only the data strictly necessary for a stated purpose, combined with analytical techniques that extract insight without exposing individual-level records.
Social Trust Mechanisms
Social trust mechanisms capture the interpersonal and community-level signals that shape how individuals evaluate the trustworthiness of digital platforms. Unlike technical or institutional indicators, these cues operate through social proof, peer endorsement, and collective governance. They draw on foundational trust research (Lewicki & Bunker, 1995; Mayer et al., 1995) and extend it into digitally mediated environments where users rely on the visible behaviour of others to calibrate their own risk assessments. The 17 cues in this construct span privacy signalling, reputation intermediaries, community self-regulation, and content integrity safeguards.
THE 17 SOCIAL TRUST MECHANISMS CUES (ST01-ST17)
ST01: Privacy Indicators & Data Access Transparency | ST02: Data Security & Secure Storage | ST03: Affiliation & Sense of Belonging | ST04: Reputation Systems & 3rd-Party Endorsements | ST05: Brand Ambassadors & Influencer Partnerships | ST06: Customer Testimonials & User-Generated Content | ST07: Community Moderation & Governance | ST08: Social Translucence & “Social Mirror” | ST09: Events & Sponsorships | ST10: Media Coverage & Press Mentions | ST11: Comparative Benchmarks & Reviews | ST12: Content Integrity & Misinformation Safeguards | ST13: Flagging & Reporting Mechanisms | ST14: Community Voting & Collective Decision-Making | ST15: Block/Ignore & Safe-Space Features | ST16: Public Interest & Crisis-Response Alerts | ST17: Co-creation & Community Engagement
ST03: Affiliation & Sense of Belonging
Trust formation is accelerated when users perceive shared identity with a platform’s community. Lewicki and Bunker (1995) demonstrated that identification-based trust represents the most resilient form of interpersonal trust, grounded in mutual understanding and emotional connection rather than rational calculation. Einwiller et al. (2000) extended this finding to online environments, showing that perceived community membership reduces the psychological distance between user and provider. When a platform cultivates belonging through shared rituals, language, or group identity markers, users internalise the platform’s interests as partially their own.
Design features that foster shared identity, group membership cues, and emotional attachment between users and the platform community.
Engender: Users who feel they belong to a community advocate for the platform voluntarily, tolerate occasional service failures, and contribute content that reinforces collective norms.
Erode: Exclusionary dynamics, opaque membership hierarchies, or algorithmic segmentation that fragments the community into isolated silos undermine the sense of shared purpose that belonging requires.
ST04: Reputation Systems & 3rd-Party Endorsements
Reputation mechanisms serve as trust proxies in environments where direct experience is unavailable. Pavlou and Gefen (2004) showed that feedback-driven reputation systems significantly reduce perceived risk in online marketplaces by aggregating the experiences of prior transactors. Josang et al. (2007) formalised computational trust models that translate discrete ratings into continuous trust scores. However, the relationship is not uniformly positive: Hoffmann et al. (2014) found that digitally native users exhibit scepticism toward conventional endorsement signals, suggesting that over-reliance on badges and seals may produce diminishing or even negative returns for younger cohorts.
Aggregated user ratings, trust seals, certification badges, and independent third-party endorsements that signal platform or seller reliability.
Engender: Transparent, manipulation-resistant rating systems lower the entry barrier for new users and enable trust transfer from established reviewers to unfamiliar offerings.
Erode: Fake reviews, purchased endorsements, or inflated ratings that become publicly exposed trigger a trust collapse disproportionate to the original deception, as users generalise the fraud to the entire reputation infrastructure.
ST06: Customer Testimonials & User-Generated Content
User-generated content functions as a decentralised credibility signal that circumvents the persuasion-knowledge filter users apply to corporate messaging. Bart et al. (2005) found that testimonials and peer narratives are among the strongest predictors of online trust, particularly for experience goods where quality cannot be assessed prior to consumption. The persuasive power of testimonials resides in their perceived authenticity: they are valued precisely because they appear to lack strategic intent. Platforms that surface unedited user stories, including critical ones, signal confidence in their own offering.
Authentic peer reviews, customer stories, and user-contributed media that provide social proof of platform value and reliability.
Engender: A visible corpus of genuine, unfiltered user experiences builds cumulative credibility and provides prospective users with relatable reference points for their own risk assessment.
Erode: Censoring negative testimonials, astroturfing with fabricated accounts, or selectively amplifying only positive content signals editorial manipulation and invites suspicion of the entire testimonial ecosystem.
ST07: Community Moderation & Governance
Self-governing communities produce trust through visible norm enforcement. Erickson and Kellogg (2000) argued that effective online communities require mechanisms that make social norms, roles, and behavioural expectations legible to participants. When moderation is exercised by community members rather than opaque algorithmic systems, users perceive governance as legitimate and participatory. The presence of transparent moderation rules, elected moderators, and published enforcement logs transforms a platform from a service into a social contract.
Community-led governance structures, transparent moderation policies, and participatory rule-making that give users agency over platform norms.
Engender: Distributed moderation with clear escalation paths and public accountability fosters collective ownership, encouraging users to invest in maintaining community standards.
Erode: Arbitrary content removal, inconsistent enforcement, or centralised moderation decisions made without community input breed resentment and drive users toward alternative platforms where governance feels more equitable.
ST08: Social Translucence & “Social Mirror”
Social translucence describes the design principle of making participants and their activities visible to one another within a digital system. Erickson and Kellogg (2000) identified three pillars of socially translucent systems: visibility, awareness, and accountability. When users can see who else is present, what actions others are taking, and how the community responds to those actions, they calibrate their own behaviour accordingly. This “social mirror” effect reproduces the informal regulatory mechanisms of physical spaces, where the mere awareness of being observed encourages cooperative conduct.
Interface elements that reveal user presence, activity patterns, and community dynamics, enabling mutual awareness and informal social regulation.
Engender: Activity indicators, contribution histories, and visible interaction patterns create a shared awareness that encourages prosocial behaviour and reduces free-riding.
Erode: Excessive surveillance, permanent behavioural tracking without consent, or weaponising visibility data for competitive ranking transforms a trust-building mechanism into a coercive monitoring tool.
ST12: Content Integrity & Misinformation Safeguards
The proliferation of synthetic media and coordinated disinformation campaigns has elevated content integrity from a moderation concern to a foundational trust requirement. The Coalition for Content Provenance and Authenticity (C2PA, 2022) established technical standards for cryptographic provenance metadata that allows users to verify the origin and edit history of digital content. Kirk and Givi (2025) demonstrated that users who encounter provenance-verified content exhibit significantly higher trust in the hosting platform, even when the content itself is critical. Platforms that invest in verifiable content pipelines signal a commitment to epistemic responsibility that extends beyond their own commercial interests.
Technical and editorial safeguards that verify content provenance, flag manipulated media, and protect users from deliberate misinformation.
Engender: Provenance labelling, fact-check overlays, and transparent editorial policies demonstrate that the platform prioritises informational accuracy over engagement metrics.
Erode: Allowing viral misinformation to persist unchallenged, applying content labels inconsistently across political or commercial lines, or deploying integrity tools selectively signals that the platform treats truth as negotiable.
ST01: Privacy Indicators & Data Access Transparency
Visual and interactive signals that communicate what data is collected, who can access it, and how users can review or revoke permissions in real time.
ST02: Data Security & Secure Storage
Visible assurances of encryption, secure infrastructure, and data handling practices that reduce user anxiety about unauthorised access or breach exposure.
ST05: Brand Ambassadors & Influencer Partnerships
Strategic alignments with trusted public figures or domain experts whose personal credibility transfers to the platform through association and endorsement.
ST09: Events & Sponsorships
Physical and virtual events, hackathons, or sponsored gatherings that create direct interpersonal contact between platform representatives and user communities.
ST10: Media Coverage & Press Mentions
Independent editorial coverage in recognised publications that provides external validation and introduces the platform to audiences beyond its existing user base.
ST11: Comparative Benchmarks & Reviews
Side-by-side evaluations by independent analysts or consumer organisations that position the platform within a competitive landscape using standardised criteria.
ST13: Flagging & Reporting Mechanisms
User-facing tools that allow community members to report harmful content, suspicious accounts, or policy violations, with visible follow-up and resolution tracking.
ST14: Community Voting & Collective Decision-Making
Mechanisms that allow users to vote on feature priorities, policy changes, or content curation decisions, distributing governance authority across the community.
ST15: Block/Ignore & Safe-Space Features
User-controlled boundary tools that allow individuals to limit unwanted interactions, mute disruptive participants, and curate their own experience without platform intervention.
ST16: Public Interest & Crisis-Response Alerts
Timely, authoritative notifications during security incidents, data breaches, or public safety events that demonstrate the platform’s commitment to user welfare over reputational management.
ST17: Co-creation & Community Engagement
Structured programmes that invite users to contribute to product development, content creation, or governance design, reinforcing shared ownership and mutual investment.
T he governance layer forms the organizational backbone of digital trust. Governance determines whether systems are operated responsibly, monitored continuously, and adapted to evolving risks and societal expectations. Traditional governance, risk, and compliance (GRC) structures assume stable processes, linear causality, and periodic oversight. These assumptions break down in complex digital environments characterized by emergent behaviors, interconnected risks, and rapidly evolving AI systems (Snowden & Boone, 2007; Dekker, 2011).
Modern governance must therefore be adaptive rather than prescriptive. Research in complexity science, resilience engineering, and socio-technical systems demonstrates that trustworthy organizations continuously sense their environment, detect weak signals, coordinate across functional boundaries, and update governance controls dynamically (Hollnagel et al., 2006; Woods, 2015). This shift aligns with recent frameworks advocating Governance–Resilience–Assurance (GRA) rather than GRC as the appropriate structure for digital ecosystems (Bengio et al., 2025; Linkov & Kott, 2019).
Three governance capabilities are critical:
Adaptive Governance
Adaptive Governance ensures that policies, design requirements, and operational practices evolve in response to emerging risks, public expectations, and regulatory change. Studies in digital governance emphasize the need for continuous policy updating, participatory decision-making, and alignment with organizational values (Floridi & Cowls, 2019).
Organizational Resilience
Organizational Resilience enables systems and teams to absorb disruptions, recover quickly, and maintain dependable service. Evidence from resilience engineering and cybersecurity research shows that resilient organizations prevent minor incidents from escalating, learn from near misses, and maintain graceful extensibility under stress (Hollnagel, 2011).
Continuous Digital Assurance
Continuous Digital Assurance refers to the set of evidence-producing mechanisms that demonstrate an AI system is functioning safely, fairly, and as intended. Techniques such as runtime monitoring, drift detection, explainability analysis, and automated compliance checks transform assurance from a periodic activity into an ongoing governance function (NIST, 2023; Raji et al., 2020). In contemporary AI governance, assurance is no longer treated as a one-off validation step but as a continuous socio-technical process embedded throughout the AI lifecycle.
THE 23 GOVERNANCE CUES (GOV01-GOV23)
GOV01: Principle-Based Trust Foundations | GOV02: AI Lifecycle Risk Assessment | GOV03: Governance Requirements Translation | GOV04: Three Lines of Defense & Accountability | GOV05: Adaptive Policy & Regulatory Alignment | GOV06: Cross-Functional Trust Ownership | GOV07: Incident Response & Crisis Management | GOV08: Graceful Degradation & Failsafe Design | GOV09: Anticipatory Monitoring & Early Warning | GOV10: Operational Continuity & Recovery | GOV11: Learning from Failures & Near Misses | GOV12: Adversarial Robustness & Red-Teaming | GOV13: Runtime Monitoring & Drift Detection | GOV14: Verifiable Data Governance | GOV15: Bias & Fairness Auditing | GOV16: Transparency Reporting & Explainability | GOV17: Independent Audit & Third-Party Verification | GOV18: Stakeholder Engagement & Participatory Oversight | GOV19: Embedded Compliance | GOV20: Sentiment Analysis & Trust Erosion Detection | GOV21: LLM Truthfulness & Safety | GOV22: Machine Ethics Auditing | GOV23: Uncertainty Communication & Expectation Management
Adaptive Governance
Structures and policies that translate ethical principles into operational governance across the AI lifecycle (Floridi & Cowls, 2019; IIA Three Lines Model, 2020).
- GOV01: Principle-Based Trust Foundations
Codified ethical principles and organisational values that serve as the normative anchor for all AI governance decisions, ensuring trust is grounded in explicit commitments rather than ad hoc judgements. - GOV02: AI Lifecycle Risk Assessment
Structured risk identification, analysis, and evaluation at each stage of the AI lifecycle, from data acquisition through deployment and decommissioning. - GOV03: Governance Requirements Translation
Conversion of high-level regulatory obligations, ethical frameworks, and stakeholder expectations into concrete, testable governance controls that engineering teams can implement. - GOV04: Three Lines of Defense & Accountability
Allocation of governance responsibilities across operational management (first line), risk and compliance functions (second line), and independent assurance (third line). - GOV05: Adaptive Policy & Regulatory Alignment
Governance policies that evolve in response to shifting regulatory landscapes, emerging standards, and new risk intelligence, rather than remaining static between periodic reviews. - GOV06: Cross-Functional Trust Ownership
Distribution of trust stewardship across business, technical, legal, and ethics functions so that no single team bears sole responsibility, fostering collective accountability.
Organisational Resilience
Capacities that enable an organisation to absorb shocks, adapt to disruption, and sustain trustworthy AI operations under adversity (Hollnagel et al., 2006; Hollnagel, 2011; Woods, 2015).
- GOV07: Incident Response & Crisis Management
Escalation pathways, communication protocols, and remediation procedures that activate when AI systems cause harm or behave unexpectedly. - GOV08: Graceful Degradation & Failsafe Design
Engineering AI systems to reduce functionality incrementally under stress rather than failing catastrophically, preserving core safety guarantees. - GOV09: Anticipatory Monitoring & Early Warning
Forward-looking indicators and anomaly detection that surface emerging trust risks before they cross critical thresholds, enabling pre-emptive intervention. - GOV10: Operational Continuity & Recovery
Ensuring that AI-dependent processes can maintain acceptable service levels during disruption and restore full capability within defined recovery time objectives. - GOV11: Learning from Failures & Near Misses
Institutionalised post-incident review and near-miss analysis so that governance controls continuously improve based on empirical evidence of what went wrong and why. - GOV12: Adversarial Robustness & Red-Teaming
Deliberate adversarial probing, including prompt injection, data poisoning, and evasion attacks, to identify vulnerabilities before hostile actors exploit them.
Continuous Digital Assurance
Ongoing verification and validation practices that provide sustained evidence of trustworthy AI operation across technical, ethical, and societal dimensions (NIST AI RMF, 2023; Raji et al., 2020; EU AI Act, 2024).
- GOV13: Runtime Monitoring & Drift Detection
Continuous tracking of model behaviour, data distributions, and performance metrics in production to detect concept drift or performance degradation. - GOV14: Verifiable Data Governance
Provenance tracking, lineage documentation, and quality controls across the data supply chain so that the evidential basis of AI decisions remains auditable. - GOV15: Bias & Fairness Auditing
Quantitative fairness metrics and qualitative equity reviews at regular intervals to detect, measure, and remediate discriminatory patterns in AI outputs. - GOV16: Transparency Reporting & Explainability
Intelligible explanations of AI decision logic calibrated to the expertise and needs of each audience, satisfying the right to explanation under the EU AI Act. - GOV17: Independent Audit & Third-Party Verification
External, independent assessments that provide assurance that internal governance claims withstand scrutiny and are not solely self-attested. - GOV18: Stakeholder Engagement & Participatory Oversight
Structured channels for affected communities, civil society, and domain experts to contribute to governance decisions, ensuring diverse perspectives. - GOV19: Embedded Compliance
Regulatory requirements integrated directly into development workflows, CI/CD pipelines, and deployment gates so that compliance is verified continuously. - GOV20: Sentiment Analysis & Trust Erosion Detection
Monitoring of public discourse, media coverage, and stakeholder feedback to identify early signals of declining trust or reputational risk. - GOV21: LLM Truthfulness & Safety
Evaluation of large language model outputs for factual accuracy, hallucination rates, and harmful content generation, with guardrails preventing unverified claims from reaching users. - GOV22: Machine Ethics Auditing
Assessment of whether AI system behaviours align with stated ethical commitments by testing decision outputs against normative scenarios and value-sensitive edge cases. - GOV23: Uncertainty Communication & Expectation Management
Communication of confidence levels, known limitations, and boundary conditions to users, preventing overreliance on outputs that carry material uncertainty.
Institutional Legitimacy and Collective Governance
Trust also depends on how societies govern AI systems and the infrastructures underlying them. The institutional layer provides the macro-level safeguards (e.g., legal frameworks, regulatory regimes, standards bodies, certification mechanisms, and public infrastructures) that ensure trust does not rely solely on private organizations. Digital identity frameworks, safety regulations, and cross-border interoperability rules illustrate how institutions establish rights, obligations, and protections.
Recent regulatory developments, such as eIDAS 2.0, the EU AI Act, and Switzerland’s AI Action Plan, demonstrate that governments increasingly view digital trust as a public good that requires coordinated action (European Parliament & Council, 2024; Hyseni, 2023; FINMA, 2024). These institutional frameworks establish several structural requirements:
- They articulate clear governance obligations and accountability expectations for AI operators.
- They mandate transparency, safety, and risk-management practices enforceable by audits and penalties.
- They ensure interoperability and cross-border trust, enabling stable digital ecosystems.
- They protect societies against discrimination, surveillance, and misuse of personal data.
Institutional trust must also be future-safe. Public rejection of previous identity initiatives (such as Switzerland’s initial e-ID proposal) revealed that trust depends not only on present safeguards but on credible protection against future misuse. Research confirms that public trust in AI remains low, especially in advanced economies, and that citizens strongly support robust governance and regulatory oversight. Institutional legitimacy, therefore, requires safeguards that remain credible across political cycles and technological change. This call to action is supported by current research on public attitudes toward AI; Lockey and Gillespie find, in their large survey across 17 countries, low levels of public trust and acceptance of AI systems, particularly in advanced economies (2025). They find a “clear public mandate for robust governance and regulation of AI systems to mitigate risks and universal endorsement of the principles and practices of trustworthy AI across countries (Lockey & Gillespie, 2025, p.279).
The iceberg trust model differentiates between two major components that influence the formation of initial trust: trust constructs and cues/signals. Trust constructs refer to elements of the iceberg that are usually underwater. They represent the schemata that unconsciously steer our behavior. Constructs represent mechanisms driven by our hot system (see Chapter 2 for more insights into the mind of the digital consumer).
Cues or signals refer to strategic areas and design patterns companies apply to engender trust. They are above the surface and help reduce information asymmetry, as outlined in the discussion of the principal-agent theory.
The model described hereafter is primarily influenced by recent research from local institutions, such as the University of St. Gallen (Hoffman et al., 2015) and the Swiss Federal Institute of Technology in Zurich (Helbing, 2015). Furthermore, it is built on the foundation of social cognitive theory. As outlined in the last chapter, cognitive structures allow for orientation in complex decision-making situations. However, the resulting behaviours are not always rational because individuals are influenced by cognitive biases.
McKnight et al. (2002) provide a beneficial model for initial trust. Analyzing the broader literature on trust in the context of new communication technologies, they found that most established models share a combination of trusting dispositions, cognition, and willingness/intentions. Furthermore, they draw on the Theory of Reasoned Action to structure their argumentation. The theory shows that trust formation follows a catenation process. Beliefs lead to attitudes, which lead to behavioural intentions and behaviour itself.
The base of the iceberg comprises four primary constructs. Together, they describe the catenated process that forms trust and leads to trusting behaviours:

Institution-based trust:
“Institutional safeguards”
The first element that constitutes the underwater body of the iceberg is the belief that the necessary structural conditions for a positive outcome are present. This element includes requirements for a structure that makes an environment trustworthy. Such a structural element is legal protection. A decent legal framework that protects privacy supports the belief in a favourable system. McKnight compares this mechanism that can make the World Wide Web a more trusted environment with the effects of establishing justice and protection in the “wild, wild west” of the 19th century. This structural assurance makes users believe that structures are in place to promote success. A second dimension of institution-based trust is situation normality. Online users who perceive high situation normality would expect, in general, that vendors in the environment possess the required trust-building attitudes: competence, benevolence, and integrity.
Dimensions (IB01-IB04):
IB01: Structural Assurance (belief that legal, regulatory, and technological safeguards protect against risks) | IB02: Situational Normality (perception that the environment is typical, proper, and conducive to success) | IB03: Regulatory & Legal Framework (confidence in the enforceability of laws, contracts, and dispute resolution) | IB04: Intermediary & Platform Trust (trust placed in platforms or marketplaces that vouch for counterparties).

Disposition to trust:
“Trust predisposition”
The individual disposition to trust describes the extent to which an individual is willing to depend on the actions of others. This propensity is inherent in any actor in a very individual way. “All trust begins and ends with the self […]” (Kahre/Rifkin, 1997: 81). Reception of stimuli and information is influenced by a person’s attitude. In addition, individual characteristics such as age, education, and income can affect the disposition to trust.
McKnight distinguishes two subconstructs of this disposition: Faith in humanity and a trusting stance. With high faith in humanity, a person assumes that others are usually upright, well-meaning, and dependable. A trusting stance means that an actor optimistically assumes a better outcome from an interaction than he would expect based on the characteristics of the agent. Principals may trust until they are proven wrong. Obviously, trust-building strategies may differ depending on the level of trust disposition. Some users are more suspicious than others. The level of disposition to trust influences institution-based trust.
Dimensions (DT01-DT04):
DT01: Faith in Humanity (general belief that others are well-meaning and reliable) | DT02: Trusting Stance (personal inclination to extend trust initially unless given reason not to) | DT03: Risk Propensity (individual willingness to accept vulnerability in uncertain situations) | DT04: Technology Readiness & Prior Experience (comfort with technology shaped by past interactions and digital literacy).

Trusting beliefs:
Cognitive Trusting Beliefs:
“Trustworthiness perceptions”
These beliefs describe the actual perceptions of specific attributes of web vendors. Trusting Beliefs now operate through two contextually activated lenses. The human-like lens (Mayer et al., 1995) assesses Competence, Benevolence, Integrity, and Predictability. The system-like lens (Lankton, McKnight, and Tripp, 2015) assesses Functionality, Reliability, and Helpfulness. The trustor applies whichever lens fits the trustee type. For AI systems, both lenses may operate simultaneously. According to the cognitive-based trust literature, trusting beliefs may form quickly. This process is heavily influenced by the individual disposition to trust as well as by the level of institution-based trust. A user believes that the trustee has attributes that benefit him. Obviously, many attributes can be considered beneficial. The most prominent ones are beliefs about competence, benevolence, and integrity. These are the main, specific attributes E-Commerce users tend to focus on to gauge vendors. Empirical data show that trusting beliefs demonstrate statistical separation. “[…] it is possible for a consumer to believe quickly that a Web-based vendor is honest and benevolent, but not competent enough to earn the consumer’s business or vice-versa (McKight, 2002, 352). The trusting beliefs differ over time. This gives room to shape customer experience as the relationship matures.
Dimensions (TB01-TB07, Dual-Lens Architecture):
- Human-like lens (TB-H): TB01: Competence / Ability | TB02: Benevolence | TB03: Integrity | TB04: Predictability.
- System-like lens (TB-S): TB05: Functionality | TB06: Reliability | TB07: Helpfulness.
For AI systems, both lenses may operate simultaneously.
Affective Trusting Beliefs:
“Emotional trust dimension”
Affective Trusting Beliefs represent the emotional dimension of trust, grounded in McAllister’s (1995) seminal distinction between cognition-based and affect-based trust. While cognitive trust (TB) evaluates competence and integrity through rational assessment, affective trust develops through emotional bonds, perceived empathy, and relational connection. For AI systems, Glikson and Woolley (2020) demonstrated that anthropomorphic design activates emotional trust through distinct pathways. The ATB construct carries five sub-dimensions: Emotional Resonance, Perceived Empathy, Interpersonal Comfort, Affective Attachment, and Relational Interaction Design.
Dimensions (ATB01-ATB05):
ATB01: Emotional Resonance (degree to which interactions evoke emotional connection and positive affect) | ATB02: Perceived Empathy (belief that the trustee understands the trustor’s situation and responds with sensitivity) | ATB03: Interpersonal Comfort (ease and willingness to engage, including sharing sensitive information) | ATB04: Affective Attachment (emotional bond from repeated positive interactions, creating loyalty beyond rational comparison) | ATB05: Relational Interaction Design (system-level design that builds rapport through conversational strategies, active listening, and sociocultural sensitivity).
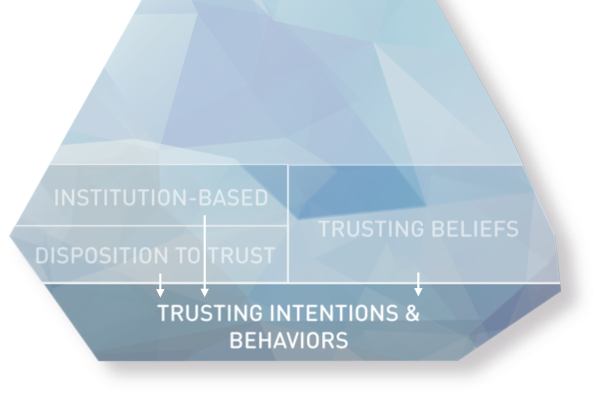
Trusting intentions and behaviours:
“Trust readiness”
Influenced by all three constructs mentioned above, a user may build an intention to engage in a trust-related behaviour and eventually act. This construct bridges the gap between cognitive assessments (trusting beliefs) and observable trust actions. Disclosing personal information to an online vendor constitutes a trust-related behaviour, as it demonstrates a willingness to be vulnerable to the vendor’s handling of sensitive data.
Dimensions (TIB01-TIB04)
TIB01: Willingness to Depend (readiness to rely on another party for important outcomes) | TIB02: Information Sharing Behavior (willingness to disclose personal or sensitive data) | TIB03: Delegation & Advice Following (willingness to delegate decisions or follow recommendations) | TIB04: Transactional Commitment (willingness to make purchases, sign contracts, or engage financially).
Relationships Between the Constructs
These four constructs relate to each other in important ways within McKnight’s framework:
Institution-based trust and disposition to trust serve as antecedents that influence trusting beliefs, particularly in new relationships where specific information about the trustee is limited.
Trusting beliefs (perceptions of trustworthiness) then lead to trusting intentions (willingness to be vulnerable), which in turn influence actual trusting behaviors.
The framework acknowledges that trusting intentions can form quickly, even in initial interactions, through cognitive processes such as categorization (stereotyping, reputation) and illusions of control, especially when supported by strong institutional safeguards. This detailed conceptualization helps explain how substantial levels of initial trust can exist without prior experience with a specific trustee, addressing a phenomenon that earlier trust models did not fully account for.

Trust is a fundamental element in human interactions, and it plays a crucial role in organisational behaviour, business relationships, and, more recently, human-technology interactions. Understanding how trust develops and evolves has been a significant focus of research across multiple disciplines. This section synthesises three significant theoretical contributions to trust development:
- Mayer, Davis, and Schoorman’s (1995) integrative model of organisational trust
- McKnight, Choudhury, and Kacmar’s work on initial trust formation (2002)
- Schlicker and colleagues’ recent Trustworthiness Assessment Model (2023, 2025)
Together, these frameworks provide a comprehensive understanding of the trust development process.
The Iceberg Trust Model is not static. Like ocean currents that reshape ice over time, three dynamic processes continuously operate on the trust constructs: trust forms through progressive stages, trust calibrates as new evidence arrives, and trust repairs (or fails to repair) after violations. These processes form the Dynamic Process Layer, a temporal overlay on the static architecture described above.
Process 1:
Trust Formation
Trust formation progresses through three stages (Lewicki and Bunker, 1995). Calculus-Based Trust is the first stage, where the trustor makes a rational cost-benefit evaluation driven primarily by above-waterline cues: reciprocity signals, brand familiarity, and visible security indicators. Knowledge-Based Trust develops through accumulated experience, as repeated interactions build Trusting Beliefs about the trustee’s competence, benevolence, and integrity. Identification-Based Trust represents the deepest stage, where shared values and identity alignment create resilient trust that can survive occasional setbacks. Not all relationships progress through all three stages. Many digital interactions remain at the calculus-based level, which is why above-waterline cue design is so critical for initial trust.
Process 2:
Trust Calibration
Trust calibration is the ongoing adjustment of perceived trustworthiness in response to new evidence (Schlicker et al., 2025; Lee and See, 2004). It depends on four factors from the Trustworthiness Assessment Model: cue relevance (is the cue diagnostic?), cue availability (is it visible?), cue detection (does the trustor notice it?), and cue utilization (does the trustor act on it?). The Contextual Moderation Layer parameterizes calibration: cultural trust radius, domain sensitivity, and user segment all influence which cues are detected and how they are weighted. De Visser et al.’s (2020) relationship equity model adds that accumulated goodwill allows systems to absorb occasional errors without triggering trust collapse. Calibration also maintains the Trust State Vector, tracking trust and distrust independently on each dimension.
Process 3:
Trust Repair
When trust is violated, different violation types require different repair strategies (Kim, Ferrin, Cooper and Dirks, 2004). Competence-based violations (the system failed at something it should do well) are best repaired through apology and corrective action, because admitting a single failure does not imply permanent incompetence. Integrity-based violations (the system or organization was dishonest or broke commitments) are best repaired through denial and evidence of principles, because admitting dishonesty confirms the worst interpretation. Tomlinson and Mayer (2009) extended this with causal attribution dimensions: locus (internal vs. external cause), controllability (could it have been prevented?), and stability (is it likely to recur?). Effective repair targets specific cracks in the Trust State Vector, aiming to restore the damaged dimension while preserving trust on intact dimensions.
The three processes operate in a continuous feedback loop. Trust forms through initial cue assessment, calibrates through ongoing experience, and repairs (or deteriorates) after violations. The outcome of repair feeds back into calibration, which updates the Trust State Vector, which in turn affects how the trustor processes future cues during the next formation cycle. The theoretical foundations for these three processes are drawn from three landmark contributions to trust research:
Mayer, Davis, and Schoorman’s Foundational Trust Model
In their seminal work, Mayer, Davis, and Schoorman (1995) proposed an integrative model of organisational trust that has become foundational in the field. They defined trust as “the willingness of a party to be vulnerable to the actions of another party based on the expectation that the other will perform a particular action important to the trustor, irrespective of the ability to monitor or control that other party” (p. 712). This definition explicitly highlights vulnerability as the critical element that distinguishes trust from related constructs such as cooperation or confidence.
The model identifies several key components in the trust development process:
First, it recognises the importance of the trustor’s propensity to trust. This propensity is a stable personality trait that represents a general willingness to trust others across situations. It influences how likely someone is to trust a trustee before receiving information about them.
Second, Mayer et al. identified three characteristics of trustees that determine their trustworthiness: ability (domain-specific skills and competencies), benevolence (the extent to which a trustee wants to do good for the trustor), and integrity (adherence to principles that the trustor finds acceptable). These three factors collectively account for a substantial portion of perceived trustworthiness.
Third, the model distinguishes between trust itself (the willingness to be vulnerable) and risk-taking in a relationship, which refers to the actual behaviours that make one vulnerable to another. A key insight is that trust leads to risk-taking behaviours only when trust exceeds the perceived risk threshold in a given situation.
Finally, Mayer et al.’s model is dynamic, with outcomes of risk-taking behaviours feeding back into assessments of the trustee’s trustworthiness. Positive outcomes enhance perceptions of trustworthiness, while negative outcomes diminish them, creating an evolving cycle of trust development.
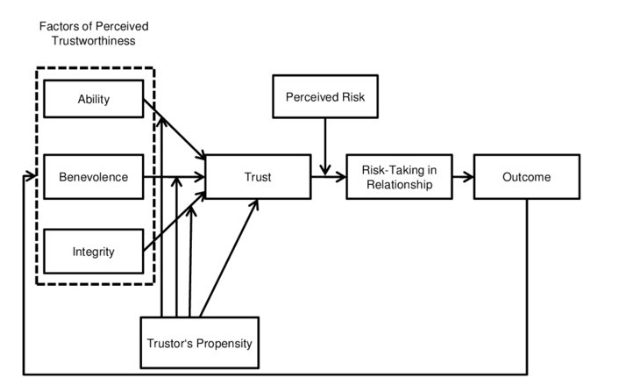
McKnight et al.’s Contributions on Initial Trust Formation
While Mayer et al.’s model effectively explains trust development over time, it does not fully account for how trust can form quickly in new relationships without prior interaction. McKnight’s work (2002) filled this gap by focusing on initial trust formation. This perspective examines how trust is established between parties who have not yet developed meaningful relationships.
As articulated in our analysis of trust constructs, McKnight introduced the concept of institution-based trust, which consists of two key elements: structural assurance (belief that structures like guarantees, regulations, or promises are in place to promote success) and situational normality (belief that the environment is proper and conducive to success). These institutional factors help explain why individuals might display high initial trust even without direct experience with a trustee.
Additionally, McKnight elaborated on the trust propensity component by distinguishing between faith in humanity (a general belief in the goodness of others) and a trusting stance (the belief that, regardless of whether others are trustworthy, trusting behaviour leads to better outcomes). This more nuanced view of propensity helps explain individual differences in initial trust formation.
McKnight’s framework also acknowledges the role of cognitive processes in rapid trust formation, including categorisation (e.g., stereotyping, reputation) and illusions of control. These processes allow trustors to make quick assessments of trustworthiness in the absence of direct experience.
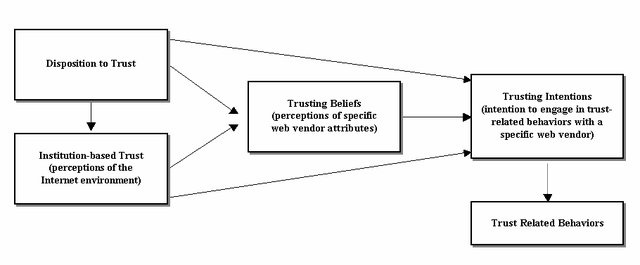
Schlicker et al.’s Trustworthiness Assessment Model
More recently, Schlicker and colleagues (2024, 2025) have developed the Trustworthiness Assessment Model (TrAM), which addresses a critical gap in previous models: the process by which a trustor’s perceived trustworthiness is formed based on a trustee’s actual trustworthiness. The TrAM makes an essential distinction between actual trustworthiness (AT) and perceived trustworthiness (PT). Actual trustworthiness represents the “true value” of a system or person’s trustworthiness relative to the trustor’s standards, while perceived trustworthiness refers to the trustor’s subjective assessment. This distinction helps explain discrepancies between a trustee’s genuine trustworthiness and how it is perceived by others.
Schlicker et al. highlight the importance of cues (Wang et al., 2004; Hoffmann et al., 2014) as the interface between actual and perceived trustworthiness. Trustors detect and utilise various cues to infer a trustee’s actual trustworthiness. The accuracy of these assessments depends on four key factors: cue relevance and availability on the trustee’s side, and cue detection and utilisation on the trustor’s side. This framework explains why different people might form different perceptions of the same trustee. Individuals may detect and interpret different cues or weight them differently.
A significant contribution of the TrAM is the emphasis on individual standards. Trust is subjective and relative to the trustor’s goals, values, and abilities in a specific context. These individual standards determine what constitutes a trustworthy entity for a specific trustor, which explains why the same characteristics might inspire trust in one person but not another.
The TrAM also operates at both micro and macro levels. At the micro level, it focuses on a single trustor assessing a specific trustee. At the macro level, it recognizes a network of assessments where different stakeholders influence each other’s trustworthiness assessments through secondary cues, creating a trustworthiness propagation process.
In their 2025 study on trust in large language model-based medical agents, Schlicker et al. further elaborated on factors influencing trustworthiness assessments. They found that benchmarking (comparing the system against human or technical alternatives), naïve theories about system functioning, risk-benefit assessments, and strategies for cue detection and utilisation all played important roles in how people assessed AI systems’ trustworthiness.
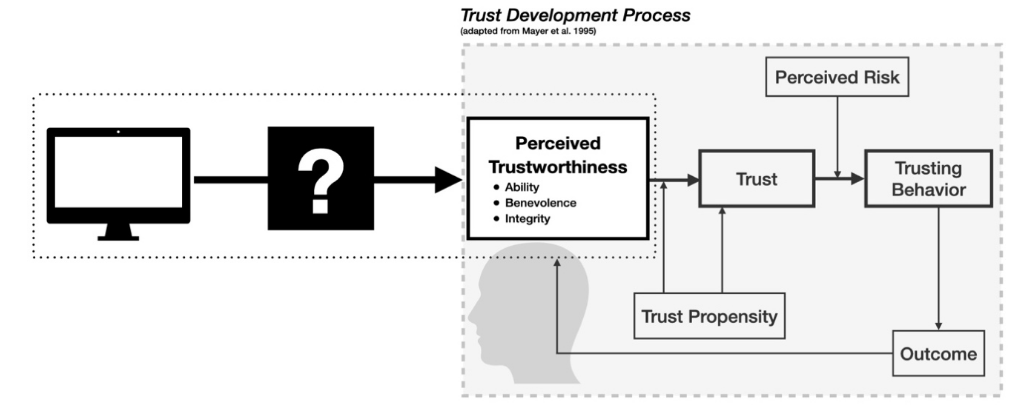
Niklas Luhmann’s systems-theoretical perspective frames trust as a dynamic interplay between trustors (e.g., users) and trustees (e.g., systems), shaped by contextual and relational factors (Luhmann, 1997; Kramer, 1999). Applied to the domain of artificial intelligence, this perspective highlights a complex network of trust relationships involving end-users, developers, organizations, and societal institutions (Castelfranchi & Falcone, 2010). Importantly, all entities, whether human or technological, are conceptualized as systems within these relationships (Lukyanenko, 2022). Consequently, trust lacks a single, universally accepted definition. The table below presents various conceptualizations of trust, each aligned with a specific type of trust relationship commonly found in the literature. Please refer to Chapter 4 for more details on the systems-theoretical perspective on trust.
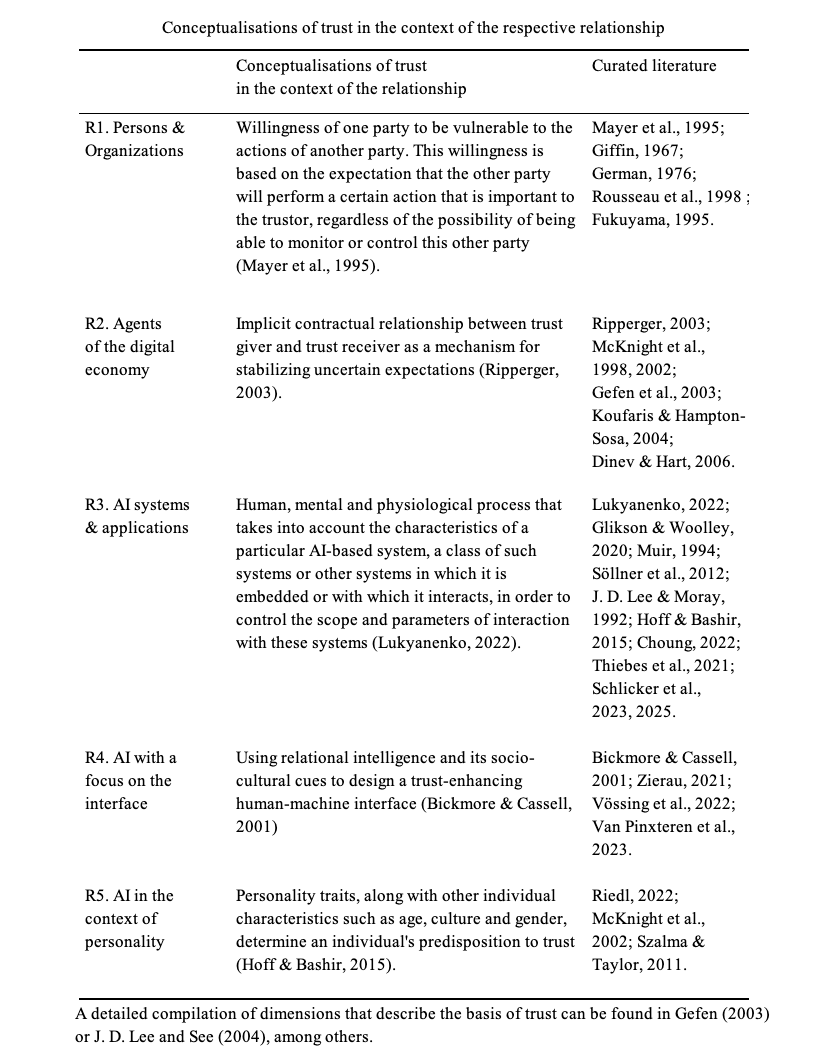
An Integrated View of Trust Development
Synthesising these three frameworks provides a comprehensive understanding of how trust develops over time.
The trustworthiness assessment occurs as trustors detect and utilise various cues to evaluate the trustee’s ability, benevolence, and integrity, forming trustworthiness perceptions. As Schlicker et al. highlighted, this assessment is filtered through the trustor’s standards and is influenced by the relevance and availability of cues, as well as the trustor’s ability to detect and properly interpret them.
Trust materialises as trust readiness, a willingness to be vulnerable, which translates to actual risk-taking behaviours when the perceived risk is acceptable. As Mayer et al. proposed, there is a threshold effect. Trust leads to risk-taking only when it exceeds the level of perceived risk in a situation.
Over time, trust evolves as outcomes of trusting behaviours feed back into perceptions of trustworthiness. Positive experiences enhance trust, while negative experiences diminish it. Additionally, Schlicker et al.’s macro-level analysis suggest that third-party assessments and secondary cues can influence a trustor’s evaluation, creating a complex social network of trust assessments.
Throughout this process, context plays a crucial role, affecting which cues are available and relevant, how they are detected and utilised, and how risk is perceived. Different domains (e.g., healthcare, finance, personal relationships) may emphasise different aspects of trustworthiness and involve different risk calculations.
Trust is a fundamental element in human interactions, and it plays a crucial role in organisational behaviour, business relationships, and, more recently, human-technology interactions. Understanding how trust develops and evolves has been a significant focus of research across multiple disciplines. This section synthesises three significant theoretical contributions to trust development:
- Mayer, Davis, and Schoorman’s (1995) integrative model of organisational trust
- McKnight, Choudhury, and Kacmar’s work on initial trust formation (2002)
- Schlicker and colleagues’ recent Trustworthiness Assessment Model (2023, 2025)
Together, these frameworks provide a comprehensive understanding of the trust development process.
The Iceberg Trust Model is not static. Like ocean currents that reshape ice over time, three dynamic processes continuously operate on the trust constructs: trust forms through progressive stages, trust calibrates as new evidence arrives, and trust repairs (or fails to repair) after violations. These processes form the Dynamic Process Layer, a temporal overlay on the static architecture described above.
Process 1:
Trust Formation
Trust formation progresses through three stages (Lewicki and Bunker, 1995). Calculus-Based Trust is the first stage, where the trustor makes a rational cost-benefit evaluation driven primarily by above-waterline cues: reciprocity signals, brand familiarity, and visible security indicators. Knowledge-Based Trust develops through accumulated experience, as repeated interactions build Trusting Beliefs about the trustee’s competence, benevolence, and integrity. Identification-Based Trust represents the deepest stage, where shared values and identity alignment create resilient trust that can survive occasional setbacks. Not all relationships progress through all three stages. Many digital interactions remain at the calculus-based level, which is why above-waterline cue design is so critical for initial trust.
Process 2:
Trust Calibration
Trust calibration is the ongoing adjustment of perceived trustworthiness in response to new evidence (Schlicker et al., 2025; Lee and See, 2004). It depends on four factors from the Trustworthiness Assessment Model: cue relevance (is the cue diagnostic?), cue availability (is it visible?), cue detection (does the trustor notice it?), and cue utilization (does the trustor act on it?). The Contextual Moderation Layer parameterizes calibration: cultural trust radius, domain sensitivity, and user segment all influence which cues are detected and how they are weighted. De Visser et al.’s (2020) relationship equity model adds that accumulated goodwill allows systems to absorb occasional errors without triggering trust collapse. Calibration also maintains the Trust State Vector, tracking trust and distrust independently on each dimension.
Process 3:
Trust Repair
When trust is violated, different violation types require different repair strategies (Kim, Ferrin, Cooper and Dirks, 2004). Competence-based violations (the system failed at something it should do well) are best repaired through apology and corrective action, because admitting a single failure does not imply permanent incompetence. Integrity-based violations (the system or organization was dishonest or broke commitments) are best repaired through denial and evidence of principles, because admitting dishonesty confirms the worst interpretation. Tomlinson and Mayer (2009) extended this with causal attribution dimensions: locus (internal vs. external cause), controllability (could it have been prevented?), and stability (is it likely to recur?). Effective repair targets specific cracks in the Trust State Vector, aiming to restore the damaged dimension while preserving trust on intact dimensions.
The three processes operate in a continuous feedback loop. Trust forms through initial cue assessment, calibrates through ongoing experience, and repairs (or deteriorates) after violations. The outcome of repair feeds back into calibration, which updates the Trust State Vector, which in turn affects how the trustor processes future cues during the next formation cycle. The theoretical foundations for these three processes are drawn from three landmark contributions to trust research:
Mayer, Davis, and Schoorman’s Foundational Trust Model
In their seminal work, Mayer, Davis, and Schoorman (1995) proposed an integrative model of organisational trust that has become foundational in the field. They defined trust as “the willingness of a party to be vulnerable to the actions of another party based on the expectation that the other will perform a particular action important to the trustor, irrespective of the ability to monitor or control that other party” (p. 712). This definition explicitly highlights vulnerability as the critical element that distinguishes trust from related constructs such as cooperation or confidence.
The model identifies several key components in the trust development process:
First, it recognises the importance of the trustor’s propensity to trust. This propensity is a stable personality trait that represents a general willingness to trust others across situations. It influences how likely someone is to trust a trustee before receiving information about them.
Second, Mayer et al. identified three characteristics of trustees that determine their trustworthiness: ability (domain-specific skills and competencies), benevolence (the extent to which a trustee wants to do good for the trustor), and integrity (adherence to principles that the trustor finds acceptable). These three factors collectively account for a substantial portion of perceived trustworthiness.
Third, the model distinguishes between trust itself (the willingness to be vulnerable) and risk-taking in a relationship, which refers to the actual behaviours that make one vulnerable to another. A key insight is that trust leads to risk-taking behaviours only when trust exceeds the perceived risk threshold in a given situation.
Finally, Mayer et al.’s model is dynamic, with outcomes of risk-taking behaviours feeding back into assessments of the trustee’s trustworthiness. Positive outcomes enhance perceptions of trustworthiness, while negative outcomes diminish them, creating an evolving cycle of trust development.
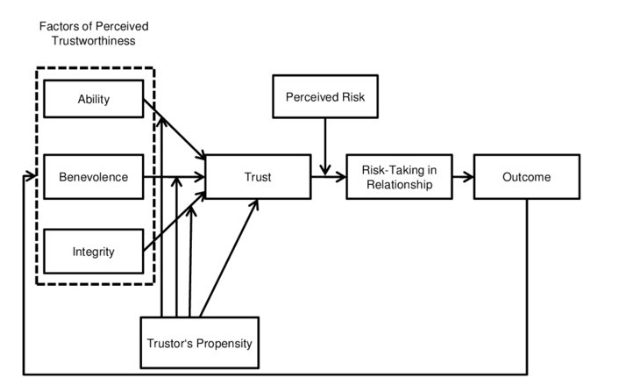
McKnight et al.’s Contributions on Initial Trust Formation
While Mayer et al.’s model effectively explains trust development over time, it does not fully account for how trust can form quickly in new relationships without prior interaction. McKnight’s work (2002) filled this gap by focusing on initial trust formation. This perspective examines how trust is established between parties who have not yet developed meaningful relationships.
As articulated in our analysis of trust constructs, McKnight introduced the concept of institution-based trust, which consists of two key elements: structural assurance (belief that structures like guarantees, regulations, or promises are in place to promote success) and situational normality (belief that the environment is proper and conducive to success). These institutional factors help explain why individuals might display high initial trust even without direct experience with a trustee.
Additionally, McKnight elaborated on the trust propensity component by distinguishing between faith in humanity (a general belief in the goodness of others) and a trusting stance (the belief that, regardless of whether others are trustworthy, trusting behaviour leads to better outcomes). This more nuanced view of propensity helps explain individual differences in initial trust formation.
McKnight’s framework also acknowledges the role of cognitive processes in rapid trust formation, including categorisation (e.g., stereotyping, reputation) and illusions of control. These processes allow trustors to make quick assessments of trustworthiness in the absence of direct experience.
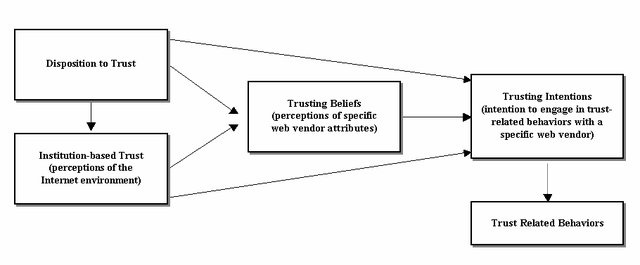
Schlicker et al.’s Trustworthiness Assessment Model
More recently, Schlicker and colleagues (2024, 2025) have developed the Trustworthiness Assessment Model (TrAM), which addresses a critical gap in previous models: the process by which a trustor’s perceived trustworthiness is formed based on a trustee’s actual trustworthiness. The TrAM makes an essential distinction between actual trustworthiness (AT) and perceived trustworthiness (PT). Actual trustworthiness represents the “true value” of a system or person’s trustworthiness relative to the trustor’s standards, while perceived trustworthiness refers to the trustor’s subjective assessment. This distinction helps explain discrepancies between a trustee’s genuine trustworthiness and how it is perceived by others.
Schlicker et al. highlight the importance of cues (Wang et al., 2004; Hoffmann et al., 2014) as the interface between actual and perceived trustworthiness. Trustors detect and utilise various cues to infer a trustee’s actual trustworthiness. The accuracy of these assessments depends on four key factors: cue relevance and availability on the trustee’s side, and cue detection and utilisation on the trustor’s side. This framework explains why different people might form different perceptions of the same trustee. Individuals may detect and interpret different cues or weight them differently.
A significant contribution of the TrAM is the emphasis on individual standards. Trust is subjective and relative to the trustor’s goals, values, and abilities in a specific context. These individual standards determine what constitutes a trustworthy entity for a specific trustor, which explains why the same characteristics might inspire trust in one person but not another.
The TrAM also operates at both micro and macro levels. At the micro level, it focuses on a single trustor assessing a specific trustee. At the macro level, it recognizes a network of assessments where different stakeholders influence each other’s trustworthiness assessments through secondary cues, creating a trustworthiness propagation process.
In their 2025 study on trust in large language model-based medical agents, Schlicker et al. further elaborated on factors influencing trustworthiness assessments. They found that benchmarking (comparing the system against human or technical alternatives), naïve theories about system functioning, risk-benefit assessments, and strategies for cue detection and utilisation all played important roles in how people assessed AI systems’ trustworthiness.
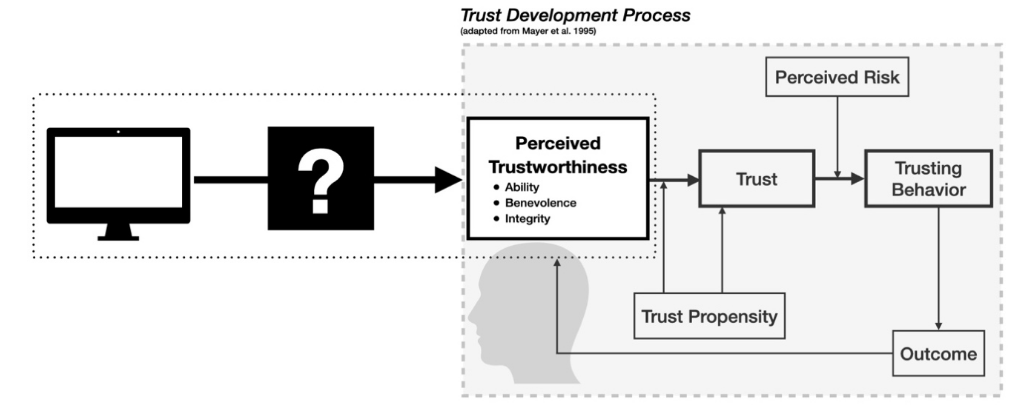
Niklas Luhmann’s systems-theoretical perspective frames trust as a dynamic interplay between trustors (e.g., users) and trustees (e.g., systems), shaped by contextual and relational factors (Luhmann, 1997; Kramer, 1999). Applied to the domain of artificial intelligence, this perspective highlights a complex network of trust relationships involving end-users, developers, organizations, and societal institutions (Castelfranchi & Falcone, 2010). Importantly, all entities, whether human or technological, are conceptualized as systems within these relationships (Lukyanenko, 2022). Consequently, trust lacks a single, universally accepted definition. The table below presents various conceptualizations of trust, each aligned with a specific type of trust relationship commonly found in the literature. Please refer to Chapter 4 for more details on the systems-theoretical perspective on trust.
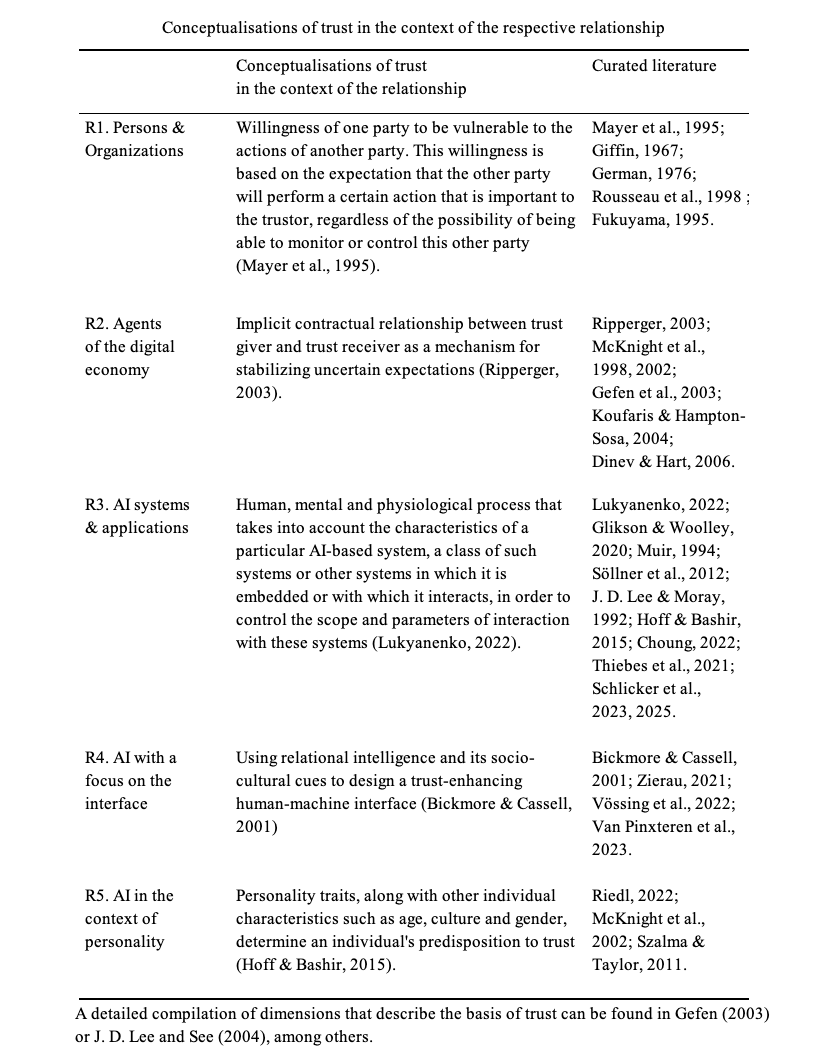
An Integrated View of Trust Development
Synthesising these three frameworks provides a comprehensive understanding of how trust develops over time.
The trustworthiness assessment occurs as trustors detect and utilise various cues to evaluate the trustee’s ability, benevolence, and integrity, forming trustworthiness perceptions. As Schlicker et al. highlighted, this assessment is filtered through the trustor’s standards and is influenced by the relevance and availability of cues, as well as the trustor’s ability to detect and properly interpret them.
Trust materialises as trust readiness, a willingness to be vulnerable, which translates to actual risk-taking behaviours when the perceived risk is acceptable. As Mayer et al. proposed, there is a threshold effect. Trust leads to risk-taking only when it exceeds the level of perceived risk in a situation.
Over time, trust evolves as outcomes of trusting behaviours feed back into perceptions of trustworthiness. Positive experiences enhance trust, while negative experiences diminish it. Additionally, Schlicker et al.’s macro-level analysis suggest that third-party assessments and secondary cues can influence a trustor’s evaluation, creating a complex social network of trust assessments.
Throughout this process, context plays a crucial role, affecting which cues are available and relevant, how they are detected and utilised, and how risk is perceived. Different domains (e.g., healthcare, finance, personal relationships) may emphasise different aspects of trustworthiness and involve different risk calculations.
The second step is central, as it involves the trustor’s evaluation of trustworthiness by identifying and interpreting relevant trust cues.
Human experience remains the most immediate and perceptually dominant layer of digital trust. Individuals evaluate a system’s trustworthiness by interpreting the cues it provides. The accuracy of this judgment depends on both the relevance and visibility of the cues provided by the system and on the human ability to correctly perceive and use those cues in forming a trust assessment (Schlicker et al., 2025). Research consistently shows that individuals infer moral intention, sincerity, and authenticity from perceived human authorship, whereas AI-mediated communication is often judged as less authentic, less caring, and less accountable (Kirk & Givi, 2025). This response reveals that trust erosion is not simply a function of content quality but of what authorship symbolizes: relational intent, human presence, normative alignment, and capacity for moral responsibility.
Conclusion
The iceberg framework of trust development presented here highlights the complex, dynamic nature of trust. Mayer et al. established the foundation with their model of trustworthiness factors and risk-taking in relationships. McKnight enhanced our understanding of initial trust formation with his concepts of institutional safeguards, trust predisposition, trustworthiness perceptions, and trust readiness. More recent studies further refined the model by illuminating the trustworthiness assessment process itself, distinguishing between actual and perceived trustworthiness, and emphasising the role of cues and individual standards.
Together, these contributions provide a rich theoretical framework for understanding how trust develops in various contexts. This understanding is increasingly important as organisations seek to build trust among employees, businesses aim to establish trust with customers, and designers of artificial intelligence systems work to create trustworthy technologies.
Trust State Vector and Dimensional Calibration
Trust Calibration maintains a dimensional trust state for each trustor-trustee relationship. Drawing on McKnight and Chervany’s (2001) finding that trust and distrust are independent dimensions, the calibration process tracks each Mayer dimension independently. In the iceberg metaphor, this manifests as cracks in the ice: when trust erodes past a threshold on one dimension while remaining intact on others, the iceberg develops visible fracture lines along dimensional boundaries.
Consider a user who has experienced a data breach from a platform they otherwise find technically competent. Their trust state might look like this: competence remains positive (the platform’s technology works well), but integrity has cracked (the platform failed to protect their data as promised). This dimensional fracture is what McKnight and Chervany (2001) predicted: trust and distrust can coexist on different dimensions of the same relationship. The user continues to use the platform for its functionality but monitors their data exposure carefully. This is “watchful trust,” a stable state that many users adopt toward technology companies they depend on but do not fully trust. “Watchful trust” (Lahusen et al., 2024) is the stable state where a user trusts the system’s competence but distrusts its integrity, resulting in active monitoring behavior.
Two lines of convergent evidence are consistent with the framework’s architecture. The Iceberg Trust Model establishes construct validity through theoretical grounding and internal consistency checking; independent empirical validation of the full framework is identified as a priority for future work.
Hoffmann, Lutz, and Meckel (2014), in a structural-equation-modeling study of online trust among German Internet users, report that reciprocity cues have a strong effect on trusting beliefs relative to other cue categories tested, and that brand cues drive behavioral intentions through a pathway distinct from trusting-beliefs formation. This study is cited as grounding for the construct-level decisions to elevate Reciprocity and Brand to distinct L1 constructs (Decisions 2 and 3); per Meehl (1978), it is not claimed simultaneously as independent validation of those same decisions, because using the same source for both discovery and confirmation is a documented circularity. Specific path coefficients and sample-size details in that study should be verified against the primary source for downstream publication.
Schlicker et al. (2025), using the Trustworthiness Assessment Model (TrAM) with a qualitative sample of 65 participants, elaborate the cue-based assessment process (relevance, availability, detection, utilization) in a way that is consistent with the above/below waterline distinction. Participants’ expectation of empathy from AI agents is consistent with the inclusion of Affective Trusting Beliefs as a distinct construct. The Schlicker study is qualitative and not a predictive test of the framework; it elaborates the assessment architecture rather than validating it.
Preliminary evidence from adjacent trust literature (Beldad, de Jong, and Steehouder, 2010; Kim, Ferrin, and Rao, 2008; Kaplan, Kessler, Brill, and Hancock, 2023, Human Factors) is also consistent with the visible-cue / hidden-belief / intention architecture used here. None of these constitutes direct predictive validation of the Iceberg Trust Model.
Knowledge about fundamental trust components and trust cues allows marketers to understand how trust is built and how businesses can interfere in this process to engender trust further. However, the discussion about customer data advocacy requires broadening horizons and extending the strategic framework with perspectives specific to data. This “data context” dimension analyses additional drivers for data advocacy. It identifies factors that individuals consider when determining if a given use of data is acceptable and that determine how users define the context of their data sharing. These research questions have attracted significant attention from political and governmental institutions. They are hotly discussed in the US White House, the US Federal Trade Commission, and the World Economic Forum.
Microsoft conducted an interesting study to establish insights into these issues and to inform the development of appropriate policy frameworks in 2012 and 2013 (Nguyen et al., 2013). The following objective variables have been recognized to impact user sensitivity in sharing personal data or trust in entities they interact with:
The results reinforced the relevance of context, indicating that what is considered acceptable use of data is personal, subject to change, and reflects differences in cultural and social norms (S. 231).

1. Type of data – what type of data it is (e.g., location, financial, medical)
2. Type of entity – who is using the data (e.g., retailer, employer, government)
3. Collection method – how the data is collected (e.g., actively provided by the user, passively collected without user awareness, inferred through analytics)
4. Device type – what kind of device is being used (e.g., mobile phone, PC)
5. Data usage – level of user involvement in the data use, from express consent to autonomous use
The Microsoft team validated the importance of each driver worldwide, noting that trust attribution varies significantly across cultural segments (refer to “consumer concerns in numbers”).
Collection methods and data usage are the two primary drivers of user sensitivity. This reflects users’ desire to control personal data, particularly in developed markets. In emerging markets, users place greater emphasis on value exchange – a factor considered a subjective trust clue within the iceberg model – than data usage. This reflects the relatively higher importance in emerging markets of perceived value for personal data provided over benefits from control.
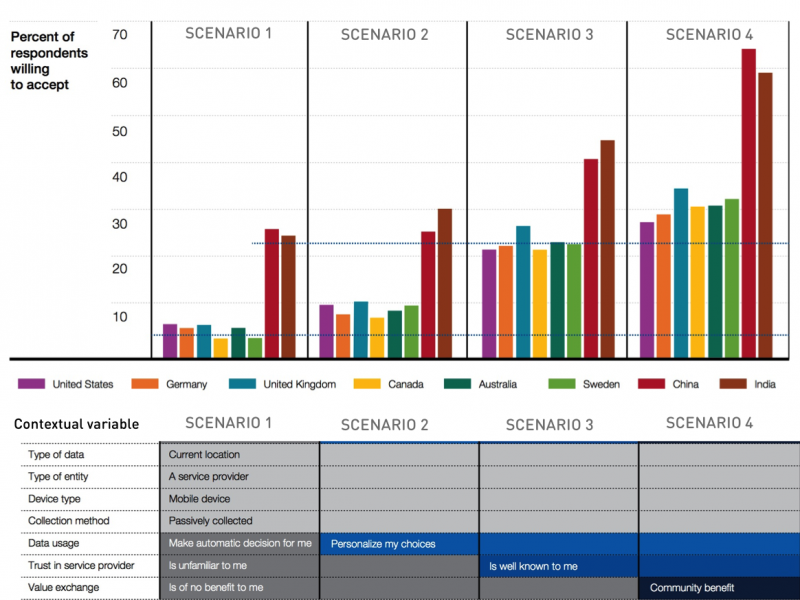
The importance of the two factors of data context, “collection method”, and “data use”, equates to today’s notice/consent model. It is best practice to collect personal data from users actively participating in the transaction, with their informed consent. However, “in the world of big data, most data will be passively collected or generated, i.e., without active user awareness, and it would be impractical if not impossible for users to give express consent with respect to all data collected” (Nguyen et al., 2013, p. 233). The remaining context variables, as well as the trust cues, can and must be leveraged to increase user acceptance to harness the potential of big data.
References Chapter 3:
Amodei, D., Olah, C., Steinhardt, J., Christiano, P., Schulman, J., & Mané, D. (2016). Concrete problems in AI safety. arXiv.org. https://arxiv.org/abs/1606.06565.
Antil, V. (2025). The end of trust: Embracing evidence-based privacy. Privado.ai. Available: https://www.privado.ai/post/the-end-of-trust-embracing-evidence-based-privacy [2025, November 22].
Bengio, Y., de Leon Ferreira de Carvalho, A. C. P., Fox, B., Nemer, M., Rivera, R. P., Zeng, Y., & Khan, S. M., et al. (2025). International AI Safety Report 2025. UK Department for Science, Innovation and Technology and AI Safety Institute. Available: https://www.gov.uk/government/publications/international-ai-safety-report-2025 [2025, November 26].
C2PA. (2022). C2PA Releases Specification of World’s First Industry Standard for Content Provenance. Coalition for Content Provenance and Authenticity. Available:
Castelfranchi, C., & Falcone, R. (2010). Trust theory: A socio-cognitive and computational model. John Wiley & Sons.
Dekker, S. (2011). Drift into failure: From hunting broken components to understanding complex systems. Ashgate. https://doi.org/10.1201/9781315257396.
Demirci, U., & Karagoz, P. (2022). Explicit and Implicit Trust Modeling for Recommendation. Digital, 2(4), 444–462. https://doi.org/10.3390/digital2040024
Deutsch, M. (1962). Cooperation and trust: Some theoretical notes. In M. R. Jones (Ed.), Nebraska Symposium on Motivation. 275–320. University of Nebraska Press.
Eagly, A. H., & Chaiken, S. (1993). The psychology of attitudes. Harcourt Brace Jovanovich.
Eccles, R., Newquist, S., & Schatz, R. (2007). Reputation and its risks. Harvard Business Review, 85, 104–114, 156. Retrieved from https://hbr.org/2007/01/reputation-and-its-risks
Einwiller, S., Geissler, U., & Will, M. (2000). Engendering trust in internet businesses using elements of corporate branding. Working Paper No. 00-04. Institute for Media and Communications Management, University of St. Gallen.
Erickson, T., & Kellogg, W. A. (2000). Social translucence: An approach to designing systems that support social processes. ACM Transactions on Computer-Human Interaction, 7(1), 59-83. https://doi.org/10.1145/344949.344958
European Parliament & Council. (2024). Regulation (EU) 2024/1183 of 11 April 2024 amending Regulation (EU) No. 910/2014 as regards establishing the European Digital Identity Framework (eIDAS 2.0). Official Journal of the European Union. Available: https://eur-lex.europa.eu/eli/reg/2024/1183/oj/eng [2025, November 24].
FINMA. (2024). Guidance 08/2024: Governance and risk management when using artificial intelligence. Available: https://www.finma.ch/en/~/media/finma/dokumente/dokumentencenter/myfinma/4dokumentation/finma-aufsichtsmitteilungen/20241218-finma-aufsichtsmitteilung-08-2024.pdf [2025, November 19].
Floridi, L., & Cowls, J. (2019). A Unified Framework of Five Principles for AI in Society. Harvard Data Science Review, 1(1). https://doi.org/10.1162/99608f92.8cd550d1.
Giddens, A. (1995). The consequences of modernity (2nd ed.). Polity Press.
Helbing, D. (Ed.). (2015). Thinking ahead—Essays on big data, digital revolution, and participatory market society. Springer. https://doi.org/10.1007/978-3-319-15078-9
Hoffmann, C. P., Lutz, C., & Meckel, M. (2014). Digital Natives or Digital Immigrants? The Impact of User Characteristics on Online Trust. Journal of Management Information Systems, 31(3), 138–171. https://doi.org/10.1080/07421222.2014.995538
Hoffmann, C. P., Lutz, C., Ranzini, G. (2024). Inequalities in privacy cynicism: An intersectional analysis of agency constraints. Big Data & Society. 11. 1-13. 10.1177/20539517241232629
Hollnagel, E., Woods, D. D., & Leveson, N. (Eds.). (2006). Resilience engineering: Concepts and precepts. Ashgate.
Hyseni, V. (2023). AI under watch: The EU AI Act. PECB Insights. Available: https://pecb.com/en/article/ai-under-watch-the-eu-ai-act [2025, November 24].
Hyseni, V. (2024). Understanding the digital trust framework. PECB Publishing. Available: https://pecb.com/en/article/understanding-the-digital-trust-framework-a-guide-for-organizations [2025, November 24].
Josang, A., Ismail, R., & Boyd, C. (2007). A survey of trust and reputation systems for online service provision. Decision Support Systems, 43(2), 618–644. https://doi.org/10.1016/j.dss.2005.05.019
Kahneman, D., & Tversky, A. (1979). Prospect theory: An analysis of decision under risk. Econometrica, 47(2), 263–291. https://doi.org/10.2307/1914185
Kahre, R., & Rifkin, J. (1997). Trust and the self: Concepts in modern consumer society. Marketing Press.
Kirk, C. P., & Givi, J. (2025). The AI-authorship effect. Journal of Business Research, 186, 114984. https://doi.org/10.1016/j.jbusres.2024.114984.
Kramer, R. M. (1999). Trust and distrust in organizations: Emerging perspectives, enduring questions. Annual Review of Psychology, 50(1), 569–598. https://doi.org/10.1146/annurev.psych.50.1.569
Linkov, I., & Kott, A. (2019). Cyber resilience of systems and networks. Springer.
Lockey, S., & Gillespie, N. (2025). Trust in AI. In S. Sadiq (Ed.), Enterprise AI. https://doi.org/10.1007/978-3-032-01940-0_10.
Luhmann, N. (1989). Vertrauen: Ein Mechanismus der Reduktion sozialer Komplexität (4th ed.). Enke.
Luhmann, N. (1997). Die Gesellschaft der Gesellschaft [The Society of Society]. Suhrkamp.
Lukyanenko, R., Maass, W. & Storey, V. C. (2022). Trust in artificial intelligence: From a Foundational Trust Framework to emerging research opportunities. Electronic Markets, 32(4), 1993–2020. https://doi.org/10.1007/s12525-022-00605-4
Marcus, G. (2020). The Next Decade in AI: Four Steps towards Robust Artificial Intelligence. arXiv.org. https://arxiv.org/abs/2002.06177.
Mayer, R. C., Davis, J. H., & Schoorman, F. D. (1995). An integrative model of organizational trust. Academy of Management Review, 20(3), 709-734. https://doi.org/10.2307/258792
McKnight, D. H., Choudhury, V., & Kacmar, C. (2002). Developing and validating trust measures for e-commerce: An integrative typology. Information Systems Research, 13(3), 334–359. https://doi.org/10.1287/isre.13.3.334.81
Nguyen, T. D., Bedford, L., & Sengupta, S. (2013). A global perspective on privacy and security: User acceptance in the new normal. Microsoft Research White Paper.
NIST. (2023). AI Risk Management Framework. National Institute of Standards and Technology. Available: https://www.nist.gov/itl/ai-risk-management-framework [2025, November 26].
Petermann, F. (1985). Vertrauen und Risikobereitschaft: Theoretische und empirische Befunde zur Sozialpsychologie des Vertrauens. Huber.
Ripperger, T. (1998). Ökonomik des Vertrauens: Analyse eines Organisationsprinzips. Mohr Siebeck.
Raji, I. D., Smart, A., White, R. N., Mitchell, M., Gebru, T., Hutchinson, B., Smith-Loud, J., Theron, D., & Barnes, P. (2020, January 3). Closing the AI accountability gap: Defining an End-to-End Framework for internal Algorithmic auditing. arXiv.org. https://arxiv.org/abs/2001.00973.
Rushkoff, D. (2017). Throwing rocks at the Google bus: How growth became the enemy of prosperity. Portfolio.
Sheehan, K. B., & Hoy, M. G. (2000). Dimensions of privacy concern among online consumers. Journal of Public Policy & Marketing, 19(1), 62–73. https://doi.org/10.1509/jppm.19.1.62.16949
Tölke, A. (2024). Trust is the key to success. Available: https://www.ti8m.com/en/blog/innovator-of-trust [2025, May 27]
ToIP. (2022). Design principles for the ToIP stack v1.0. Trust over IP Foundation. Available: https://trustoverip.org/wp-content/uploads/Design-Principles-for-the-ToIP-Stack-V1.0-2022-11-17.pdf [2025, November 24].
Wang, S., Beatty, S. E., & Foxx, W. (2004). Signaling the trustworthiness of small online retailers. Journal of Interactive Marketing, 18(1), 53-69. https://doi.org/10.1002/dir.10071
Bart, Y., Shankar, V., Sultan, F., and Urban, G. L. (2005). Are the drivers and role of online trust the same for all web sites and consumers? Journal of Marketing, 69(4), 133-152.
Doney, P. M., Cannon, J. P., and Mullen, M. R. (1998). Understanding the influence of national culture on the development of trust. Academy of Management Review, 23(3), 601-620.
Glikson, E. and Woolley, A. W. (2020). Human trust in artificial intelligence: Review of empirical research. Academy of Management Annals, 14(2), 627-660.
Guest, G., Bunce, A., and Johnson, L. (2006). How many interviews are enough? Field Methods, 18(1), 59-82.
Hancock, J. T., Naaman, M., and Levy, K. (2020). AI-Mediated Communication: Definition, Research Agenda, and Ethical Considerations. Journal of Computer-Mediated Communication, 25(1), 89-100.
Hennink, M. M., Kaiser, B. N., and Marconi, V. C. (2017). Code saturation versus meaning saturation. Qualitative Health Research, 27(4), 591-608.
Hevner, A. R., March, S. T., Park, J., and Ram, S. (2004). Design science in information systems research. MIS Quarterly, 28(1), 75-105.
Ji, Z., Lee, N., Frieske, R., Yu, T., Su, D., Xu, Y., Ishii, E., Bang, Y. J., Madotto, A., and Fung, P. (2023). Survey of Hallucination in Natural Language Generation. ACM Computing Surveys, 55(12), 1-38.
Karimi, A. H., Barthe, G., Balle, B., and Valera, I. (2021). A Survey of Algorithmic Recourse: Contrastive Explanations and Consequential Recommendations. ACM Computing Surveys, 55(5), 1-29.
Kim, P. H., Ferrin, D. L., Cooper, C. D., and Dirks, K. T. (2004). Removing the shadow of suspicion: The effects of apology versus denial. Journal of Applied Psychology, 89(1), 104-118.
Lahusen, C. et al. (2024). Trust, trustworthiness and AI governance. Scientific Reports, 14, Article 19368.
Lankton, N. K., McKnight, D. H., and Tripp, J. (2015). Technology, humanness, and trust. Journal of the Association for Information Systems, 16(10), 880-918.
McAllister, D. J. (1995). Affect- and cognition-based trust as a foundation for interpersonal cooperation. Academy of Management Journal, 38(1), 24-59.
McKnight, D. H. and Chervany, N. L. (2001). Trust and distrust definitions. In Trust in Cyber-Societies (pp. 27-54). Springer.
Nissenbaum, H. (2010). Privacy in Context: Technology, Policy, and the Integrity of Social Life. Stanford University Press.
Sandhu, R. S., Coyne, E. J., Feinstein, H. L., and Youman, C. E. (1996). Role-Based Access Control Models. IEEE Computer, 29(2), 38-47.
Shneiderman, B. (2020). Human-Centered Artificial Intelligence: Reliable, Safe & Trustworthy. International Journal of Human-Computer Interaction, 36(6), 495-504.
Strauss, A. and Corbin, J. (1998). Basics of Qualitative Research (2nd ed.). Sage.
Ustun, B., Spangher, A., and Liu, Y. (2019). Actionable Recourse in Linear Classification. Proceedings of the Conference on Fairness, Accountability, and Transparency (FAT*), 10-19.
Werbach, K. (2018). The Blockchain and the New Architecture of Trust. MIT Press.